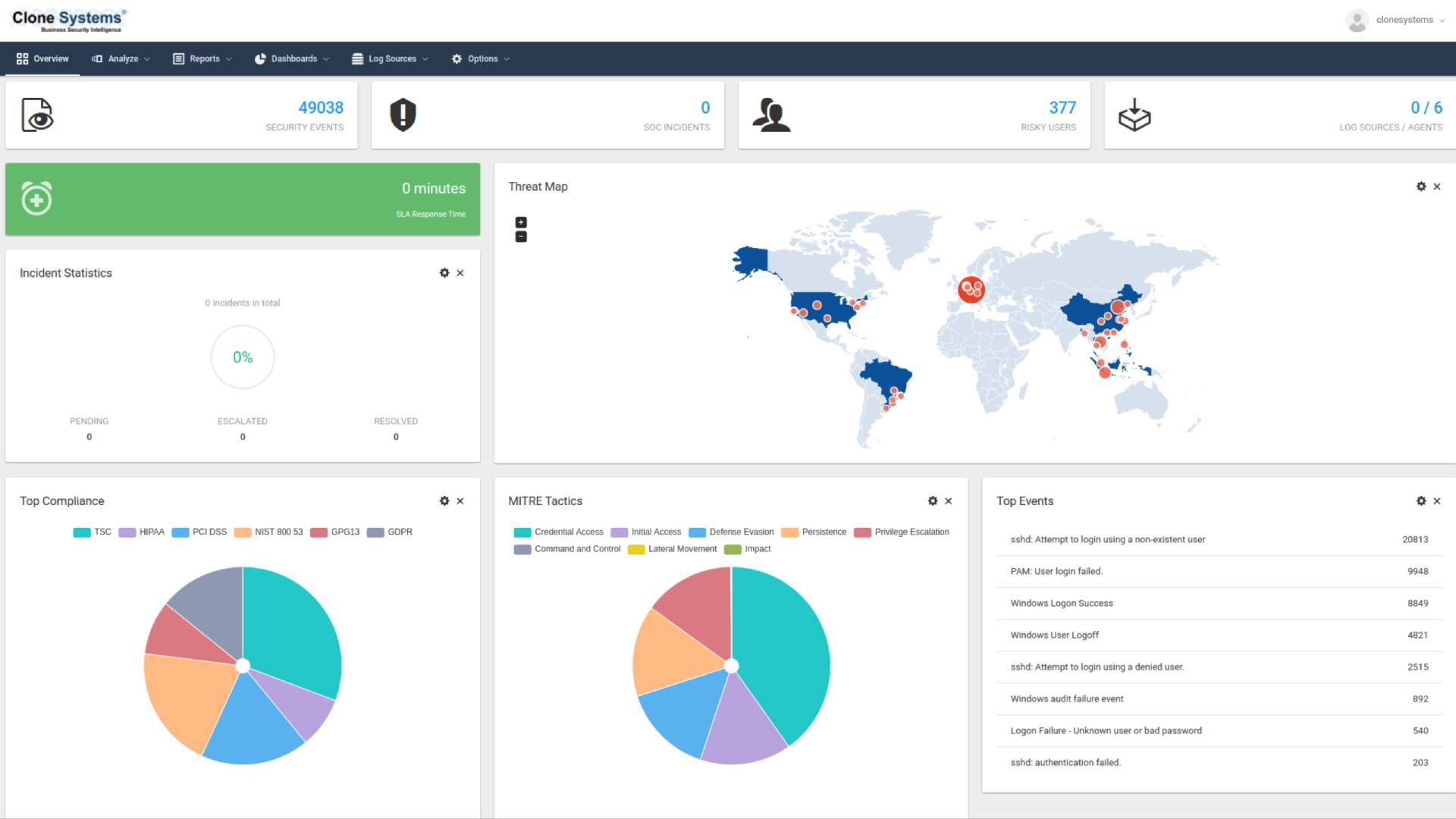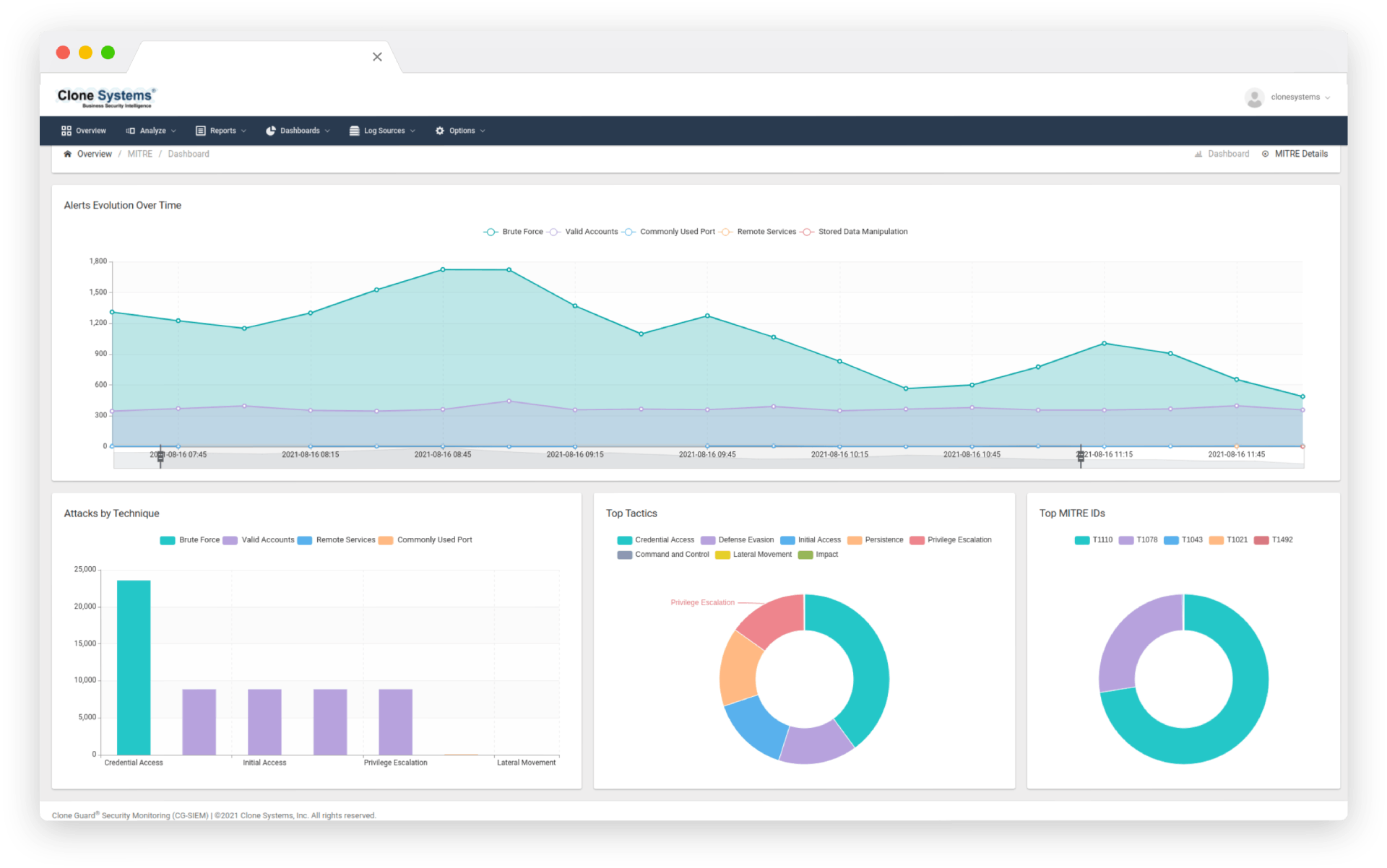
Managed SIEM and EDR Real Time Threat Detection and Response
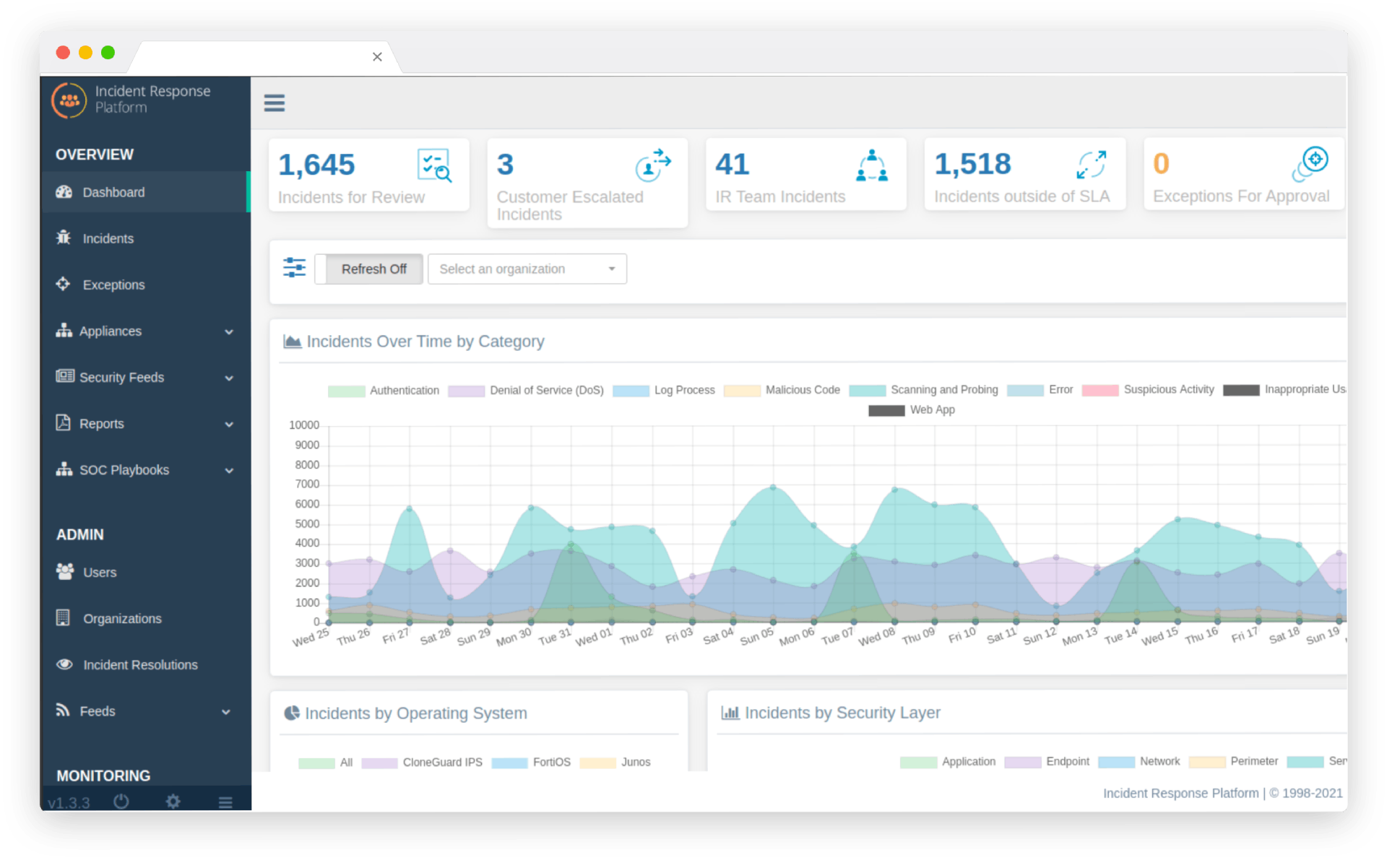
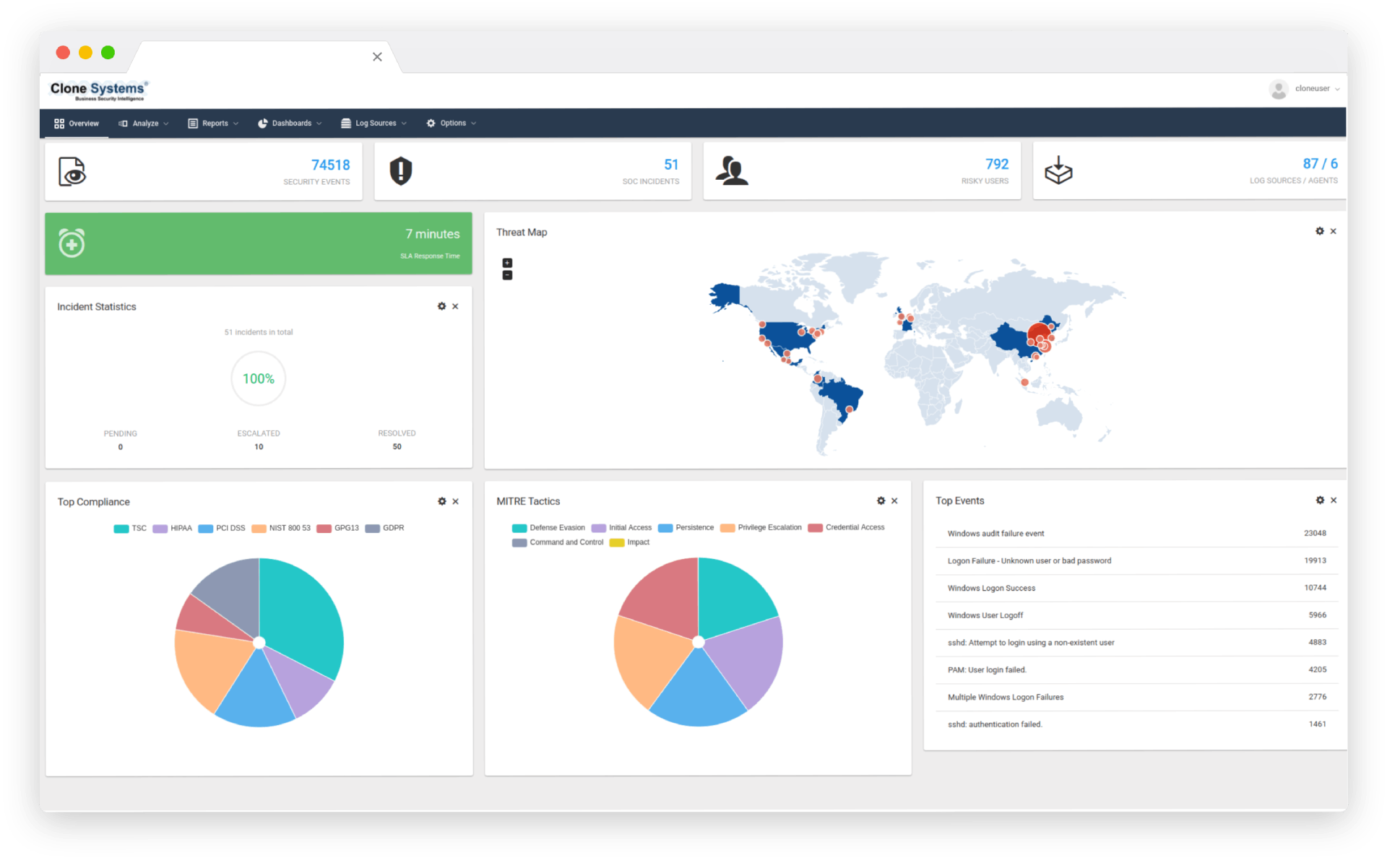
Real-time analysis of threats, by correlating historical and real-time security information and analyzing correlated events to help prevent emerging threats.
Customers Around the World
Drowning in Logs? Gain Clarity With Managed SIEM & EDR
Traditional SIEM tools can overwhelm IT teams with endless logs and alerts, and configuring them correctly requires specialized expertise. As attackers target endpoints and cloud services, organizations need unified visibility into all systems to detect and respond quickly.
Managed SIEM & EDR to the Rescue
Clone Systems’ Managed SIEM with integrated Endpoint Detection and Response centralizes log collection and analysis, correlates events across your entire environment and provides real‑time detection of malicious activity. Our security team manages the platform for you, fine‑tuning alerts so you only see what matters.
Key Capabilities of Managed SIEM & EDR
Benefits
Oututsourcing SIEM and EDR management frees your team from day‑to‑day security operations while improving your overall security posture:
- Cost Efficiency: Avoid the capital and operational expenses associated with building and maintaining your own SIEM platform.
- Rapid Deployment: Our managed service gets you up and running quickly, often in days rather than months.
- Specialized Expertise: Benefit from a team of analysts who live and breathe security monitoring.
- Reduced Risk: Continuous monitoring helps catch threats early, minimizing the potential impact on your business.
- Improved Awareness: Actionable reports and dashboards increase your organization’s security awareness and help inform strategic decisions.
How It Works
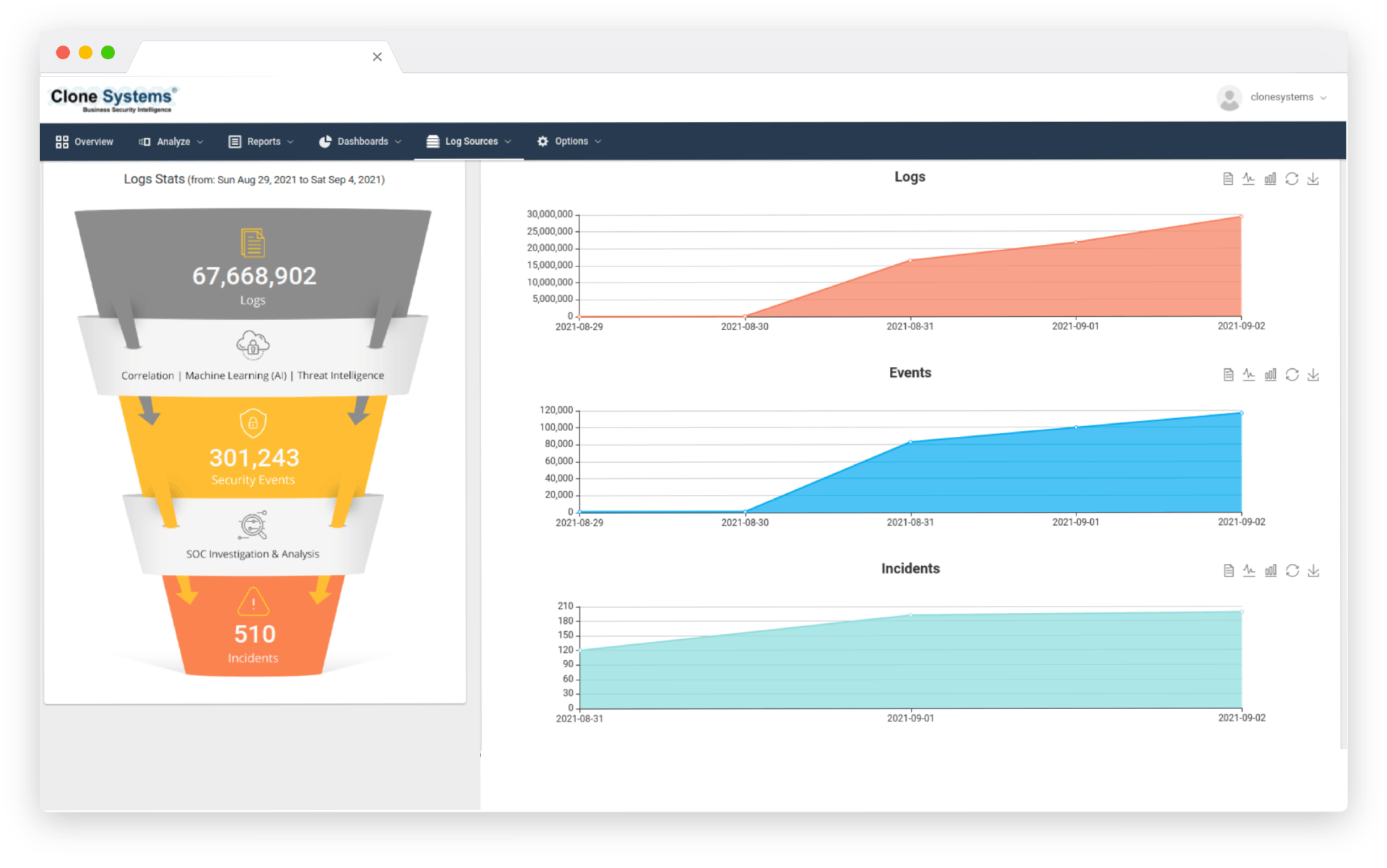
- Onboarding & Log Collection: We integrate your log sources— servers, network devices, cloud services, endpoints—into our secure platform.
- Normalization & Correlation: The system normalizes data and applies correlation rules and machine learning to detect anomalies.
- Alerting & Response: Alerts are filtered and prioritized; our analysts review high‑severity events and provide guidance.
- Reporting & Review: Regular reports summarize activity, compliance status and recommended improvements.

Security Orchestration Automation & Response (SOAR)
Automate your security operations with SOAR – our advanced solution that streamlines your incident response processes, reduces manual tasks, and enables your team to respond to potential threats quickly and effectively. With real-time threat detection and automated incident response, you can minimize the impact of cyber attacks and prevent future incidents. Contact us today to learn how SOAR can enhance your organization’s security posture.

Extended Detection and Response (XDR)
Our XDR solution delivers real-time insights and automated response actions to help you quickly identify and mitigate security incidents. With comprehensive visibility across endpoints, networks, and cloud environments, you can proactively detect and prevent attacks before they cause damage. Boost your security posture and stay ahead of evolving threats with XDR.

Log Management
Log Management is the backbone of any security strategy, enabling organizations to detect and respond to security threats before they become major incidents. With our Log Management solution, you can quickly identify security incidents, investigate root causes, and take action to remediate them. Our comprehensive reporting and analysis capabilities provide valuable insights into your security environment, allowing you to make informed decisions that enhance your overall security posture.

Endpoint Detection & Response (EDR)
Our EDR solution offers continuous monitoring and rapid response to threats, enabling you to proactively defend against attacks and minimize damage. With detailed forensic analysis and incident response capabilities, our EDR solution empowers you to quickly identify and neutralize threats before they become major incidents. Partner with us today to strengthen your endpoint security and protect your critical assets.
Security Orchestration Automation & Response (SOAR)
Automate your security operations with SOAR – our advanced solution that streamlines your incident response processes, reduces manual tasks, and enables your team to respond to potential threats quickly and effectively. With real-time threat detection and automated incident response, you can minimize the impact of cyber attacks and prevent future incidents. Contact us today to learn how SOAR can enhance your organization’s security posture.
Extended Detection and Response (XDR)
Our XDR solution delivers real-time insights and automated response actions to help you quickly identify and mitigate security incidents. With comprehensive visibility across endpoints, networks, and cloud environments, you can proactively detect and prevent attacks before they cause damage. Boost your security posture and stay ahead of evolving threats with XDR.
Log Management
Log Management is the backbone of any security strategy, enabling organizations to detect and respond to security threats before they become major incidents. With our Log Management solution, you can quickly identify security incidents, investigate root causes, and take action to remediate them. Our comprehensive reporting and analysis capabilities provide valuable insights into your security environment, allowing you to make informed decisions that enhance your overall security posture.
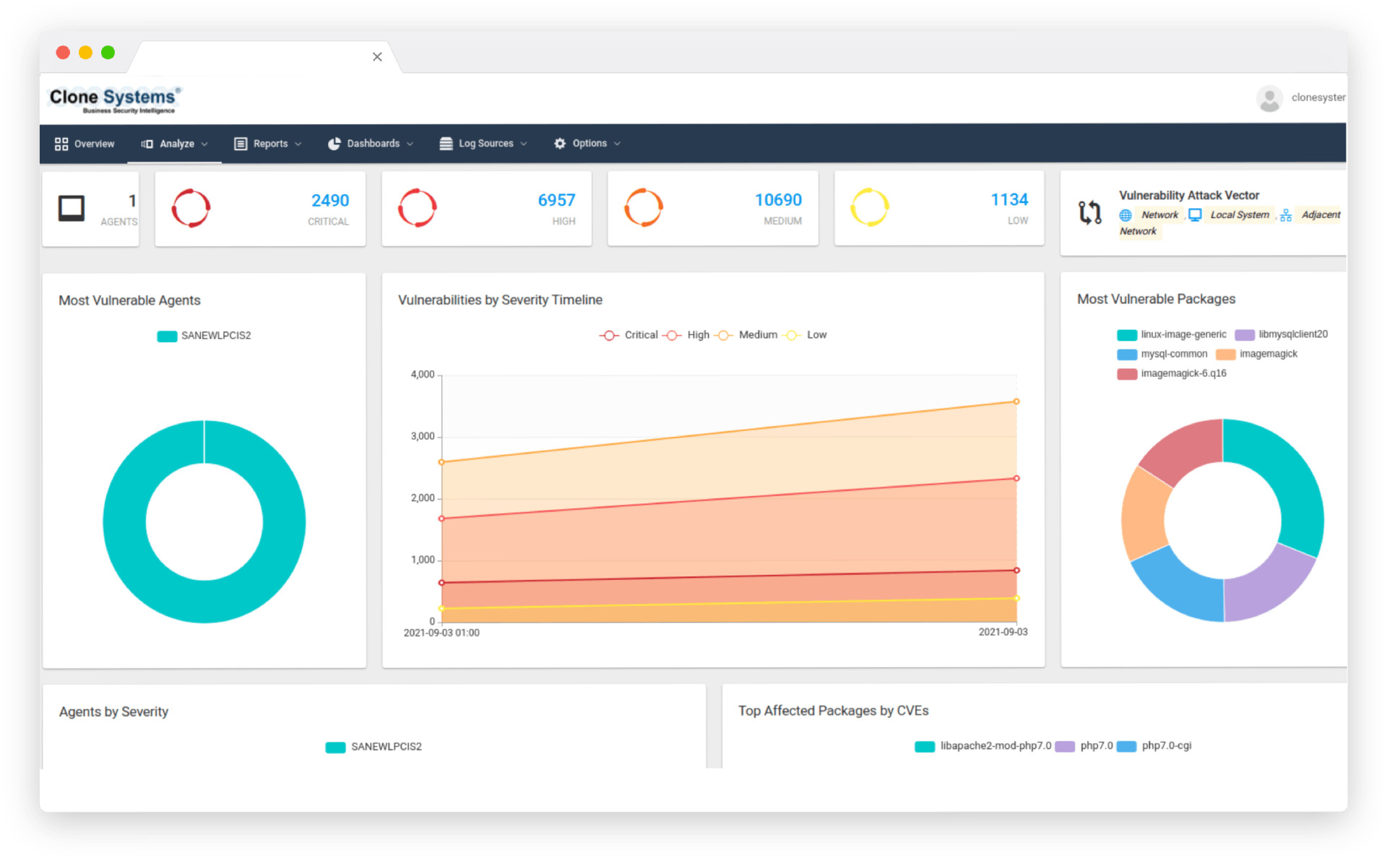
Endpoint Detection & Response (EDR)
Our EDR solution offers continuous monitoring and rapid response to threats, enabling you to proactively defend against attacks and minimize damage. With detailed forensic analysis and incident response capabilities, our EDR solution empowers you to quickly identify and neutralize threats before they become major incidents. Partner with us today to strengthen your endpoint security and protect your critical assets.