Continuous Penetration Testing Ongoing Vulnerability Discovery and Remediation
Keep your Business safe from Cyber Threats with our Continuous Penetration Testing Solution.
Continuous Penetration Testing Ongoing Vulnerability Discovery and Remediation
Keep your Business safe from Cyber Threats with our Continuous Penetration Testing Solution.
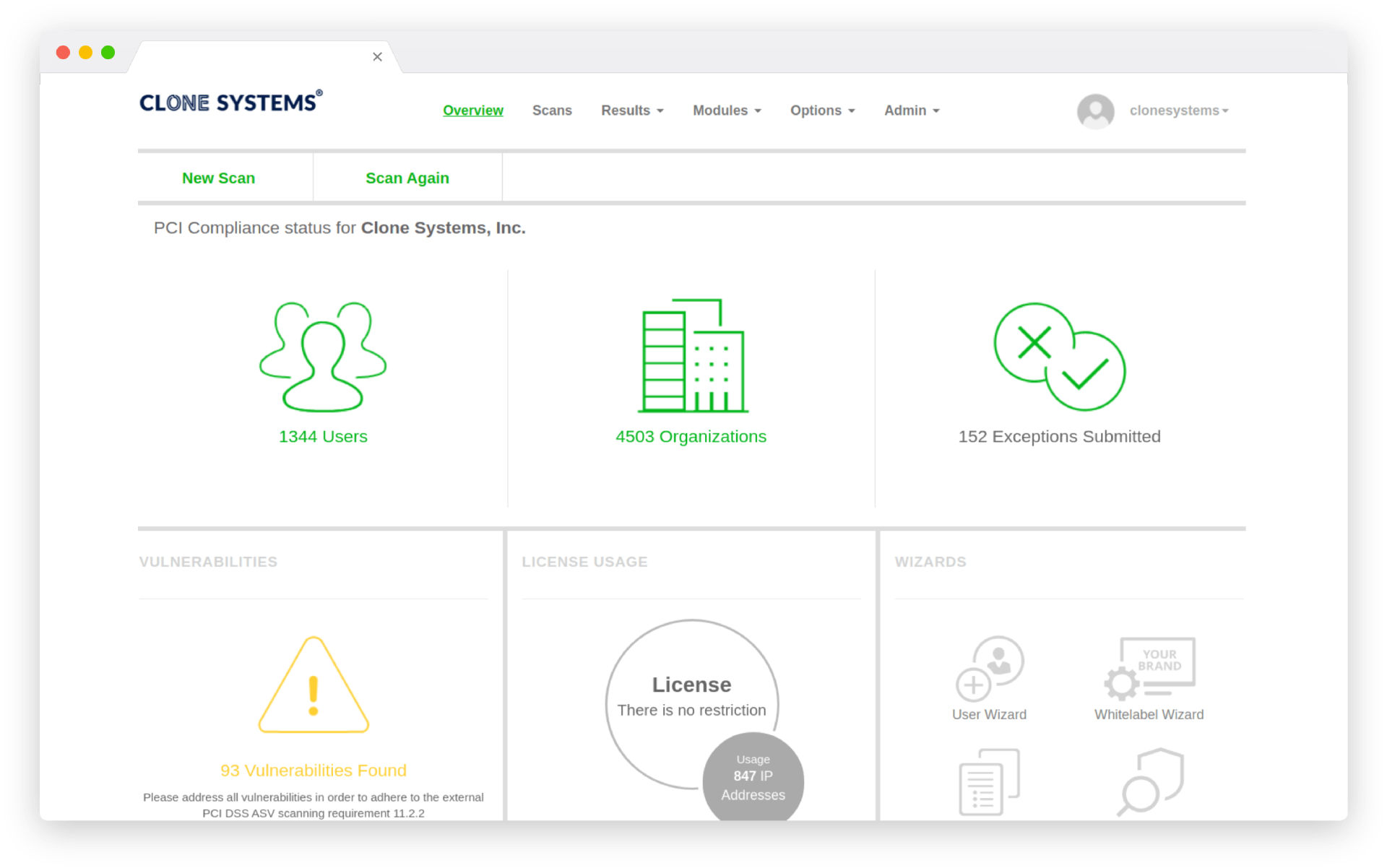
Customers Around the World
Closing the Gap Between Tests
Annual or quarterly pen tests leave long windows during which new vulnerabilities can appear. Meanwhile, development teams release updates and infrastructure changes that may introduce fresh attack paths.
Always‑On Testing for an Ever‑Evolving Attack Surface
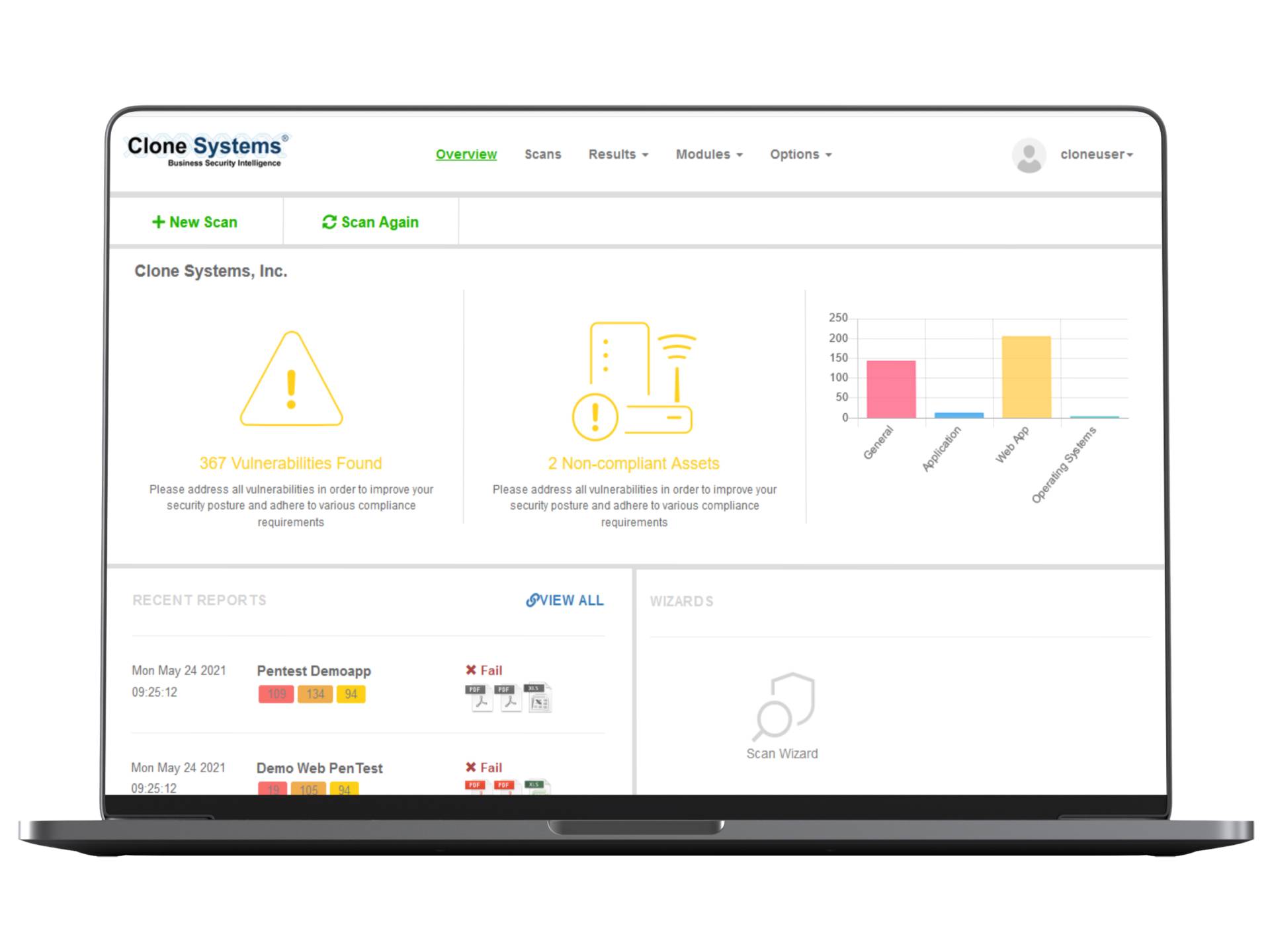
Clone Systems’ Continuous Penetration Testing (also called Continuous Attack Surface Penetration Testing) integrates automated scanning and expert analysis into your development and operations workflows. As your environment changes, tests run automatically to identify new weaknesses. Our security analysts validate findings and provide actionable advice in real time, reducing the time between discovery and remediation.
Key Features of Continuous Penetration Testing
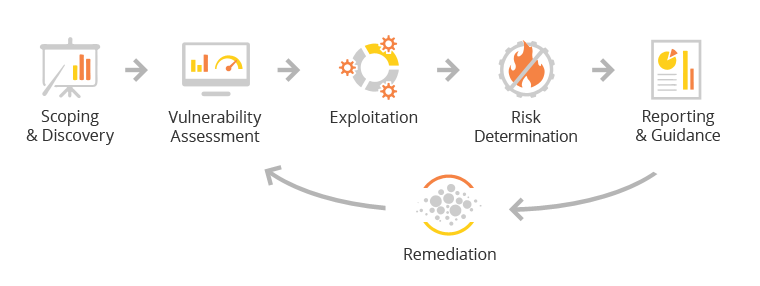
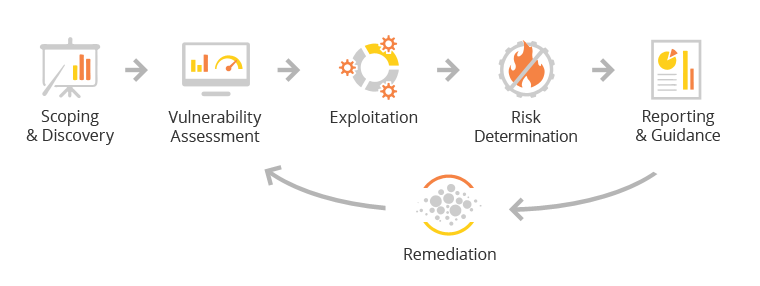
How It Works
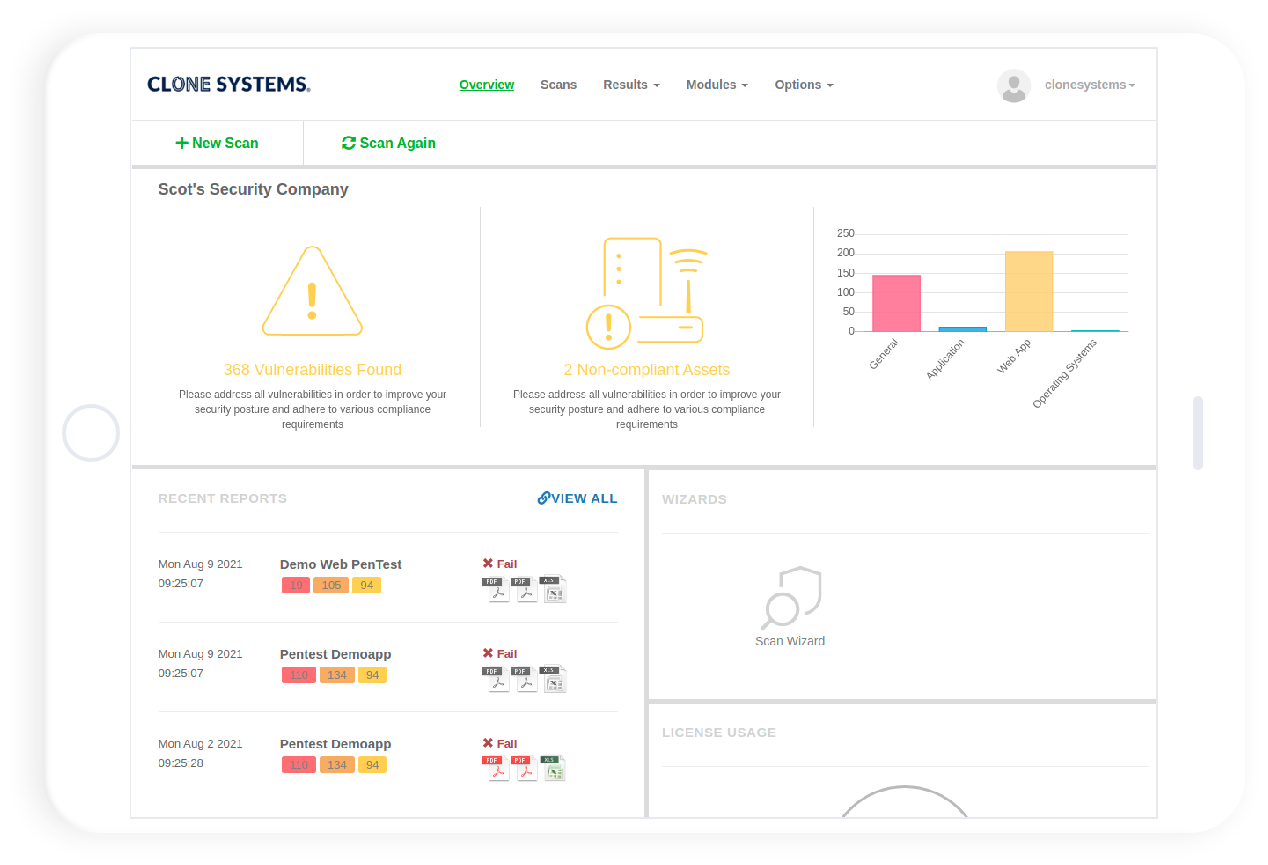
- Proactive Security Posture: Identify and fix vulnerabilities as they emerge instead of waiting for scheduled tests.
- Better Return on Investment: After the initial onboarding, subsequent tests focus on changes, reducing ramp‑up time and costs.
- Reduced Window of Exposure: Continuous monitoring shortens the time vulnerabilities are available for exploitation, lowering the overall risk.
How It Works
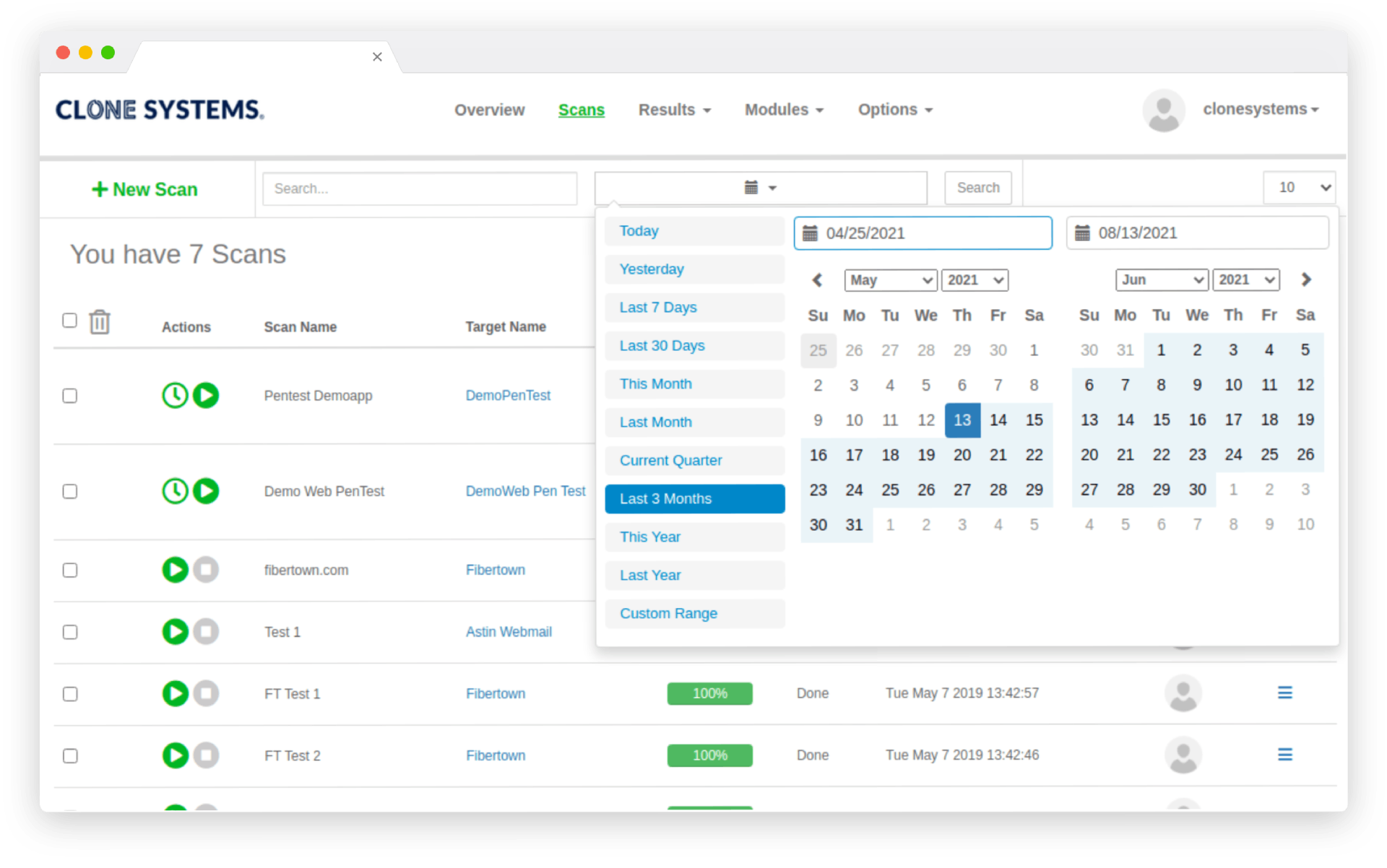
- Asset & Change Detection: Monitor your environment for new applications, infrastructure changes or code deployments.
- Automated Scanning & Human Review: Automated tools run tests against the updated attack surface; security experts review and validate results.
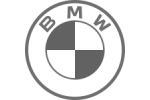
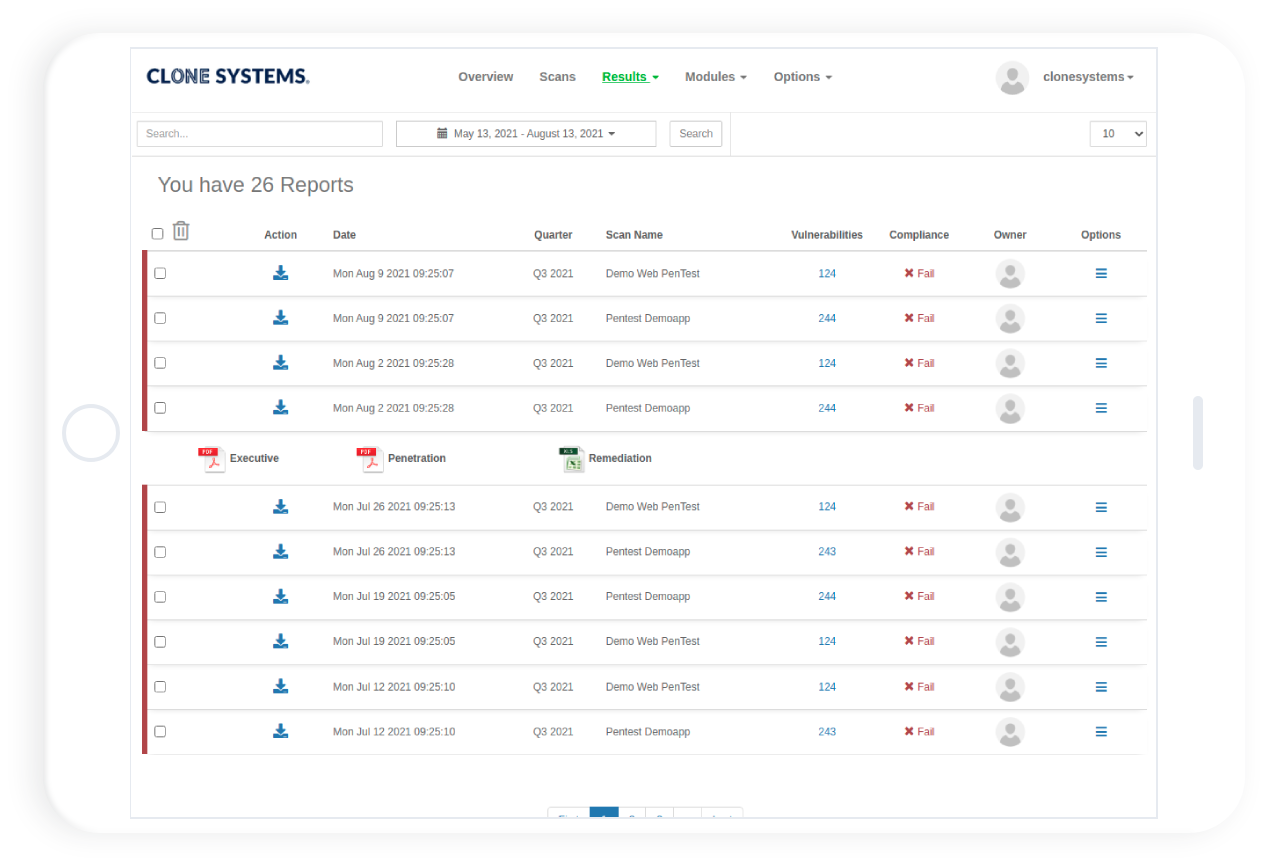
- Real‑Time Notification: Findings are delivered via dashboards and notifications, with severity ratings and remediation steps.
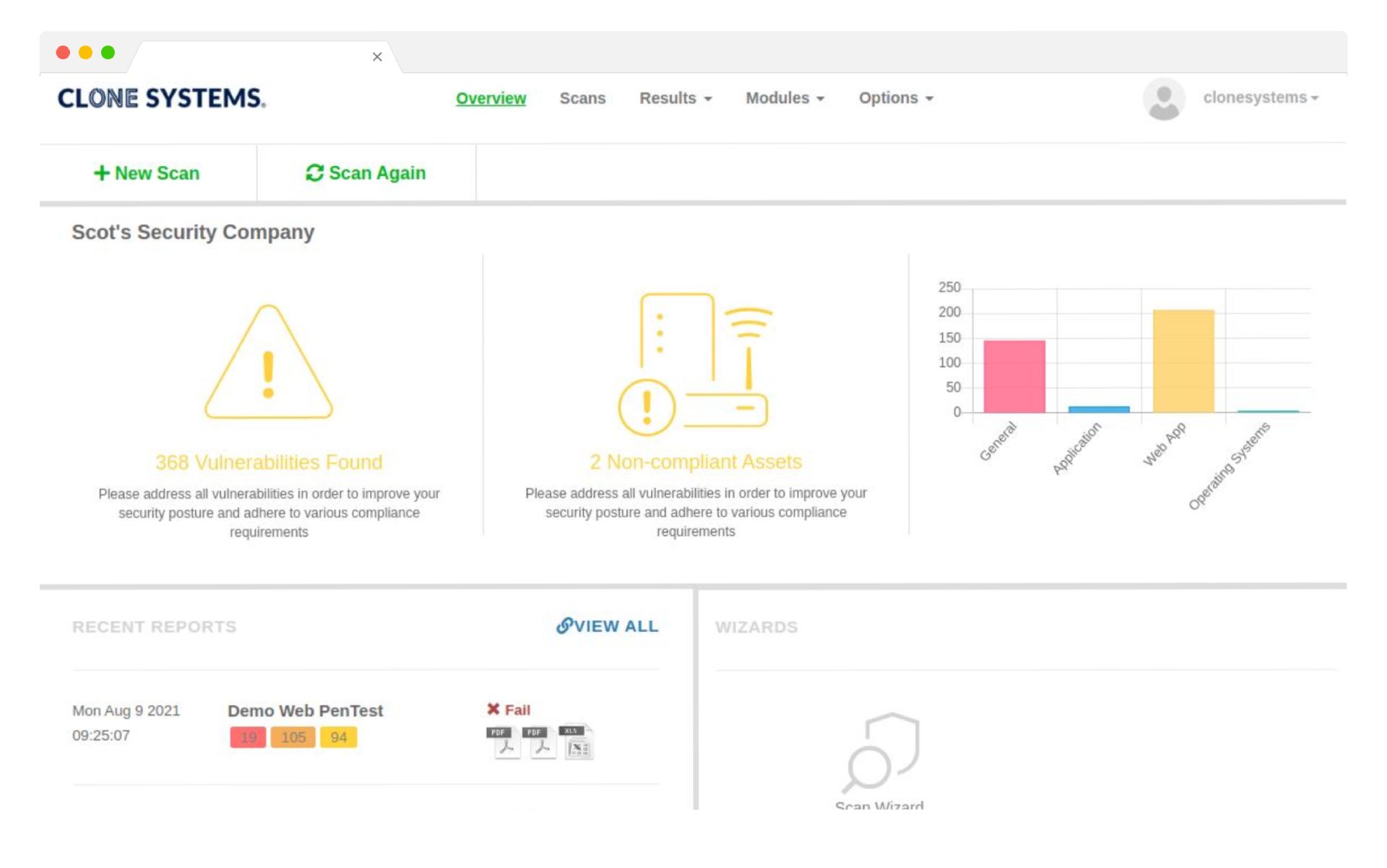
- Continuous Improvement: As vulnerabilities are fixed, the platform retests to confirm remediation and updates its baseline for future scans.
Stay ahead with regular testing
Our Continuous Penetration Testing solution provides regular security testing to help you stay ahead of the curve. With a team of experienced security professionals, we identify vulnerabilities and provide recommendations for improvement to keep your business safe from cyber threats.
Protect your business from Threats
Our comprehensive Continuous Penetration Testing solution includes both automated and manual testing to provide a complete view of your security posture. With progress reporting and recommendations for improvement, we help you stay ahead of the game and protect your business from cyber threats.
Safeguard Your Business
Our Continuous Penetration Testing solution includes a virtual or physical appliance that provides continuous security testing of your systems. With a combination of automated scanning and manual testing, we identify vulnerabilities and provide actionable recommendations for improvement to keep your business safe.
Comprehensive Security for Your Business
With our Continuous Penetration Testing solution, you’ll receive asset discovery capabilities that identify all devices on your network, providing comprehensive security testing to keep your systems secure. Our approach includes automated scanning, manual testing, and progress reporting to ensure your business is always protected.
Stay ahead with Regular Testing
Our Continuous Penetration Testing solution provides regular security testing to help you stay ahead of the curve. With a team of experienced security professionals, we identify vulnerabilities and provide recommendations for improvement to keep your business safe from cyber threats.
Protect your business from threats
Our comprehensive Continuous Penetration Testing solution includes both automated and manual testing to provide a complete view of your security posture. With progress reporting and recommendations for improvement, we help you stay ahead of the game and protect your business from cyber threats.
Safeguard Your Business
Our Continuous Penetration Testing solution includes a virtual or physical appliance that provides continuous security testing of your systems. With a combination of automated scanning and manual testing, we identify vulnerabilities and provide actionable recommendations for improvement to keep your business safe.
Comprehensive Security for Your Business
With our Continuous Penetration Testing solution, you’ll receive asset discovery capabilities that identify all devices on your network, providing comprehensive security testing to keep your systems secure. Our approach includes automated scanning, manual testing, and progress reporting to ensure your business is always protected.