Managed Penetration Testing Services Expert Led Security Assessments
One our our CISSP Engineers will perform real-world attack simulations on your infrastructure to identify threats
Talk with our experts
Managed Penetration Testing Services Expert Led Security Assessments
One our our CISSP Engineers will perform real-world attack simulations on your infrastructure to identify threats
Customers Around the World
Problem & Solution
Why Manual Testing Matters
Automated tools are valuable for broad coverage, but they cannot replicate the creativity of a skilled attacker. Complex business logic flaws, chained exploits and subtle misconfigurations often require a human assessor to find and exploit.
Deep Assessments by Ethical Hackers
Clone Systems’ Managed Penetration Testing is performed by seasoned security professionals who act like adversaries. They craft attack plans, pivot through networks and uncover vulnerabilities that automated scanners miss. The result is a detailed understanding of your exposure and practical remediation guidance.
Key Features of Our SOC Service
Benefits
Key benefits include:
- Deeper Insights: Human creativity uncovers complex vulnerabilities that automated tools overlook.
- Audit and Compliance Readiness: Third‑party assessments provide evidence for auditors and regulators.
- Skill Development: Your internal team learns from our testers’ techniques and remediation guidance.
- Confidence in Security Posture: Detailed reports provide assurance that you have thoroughly tested your defences.
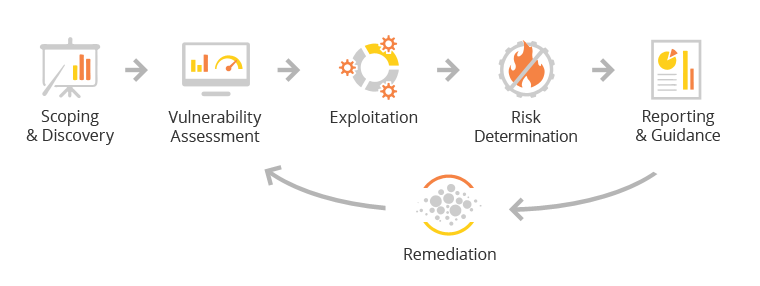
How It Works
- Scoping: Define the goals, rules of engagement, and assets to be tested.
- Reconnaissance & Enumeration: Identify open ports, services and potential attack paths.
- Exploitation: Attempt to exploit discovered weaknesses and pivot within the environment.
- Post‑Exploitation & Reporting: Document findings, gather evidence and draft a comprehensive report with remediation guidance.
- Debrief & Support: Conduct a session with your team to review findings and share best practices.
Obtain support and guidance
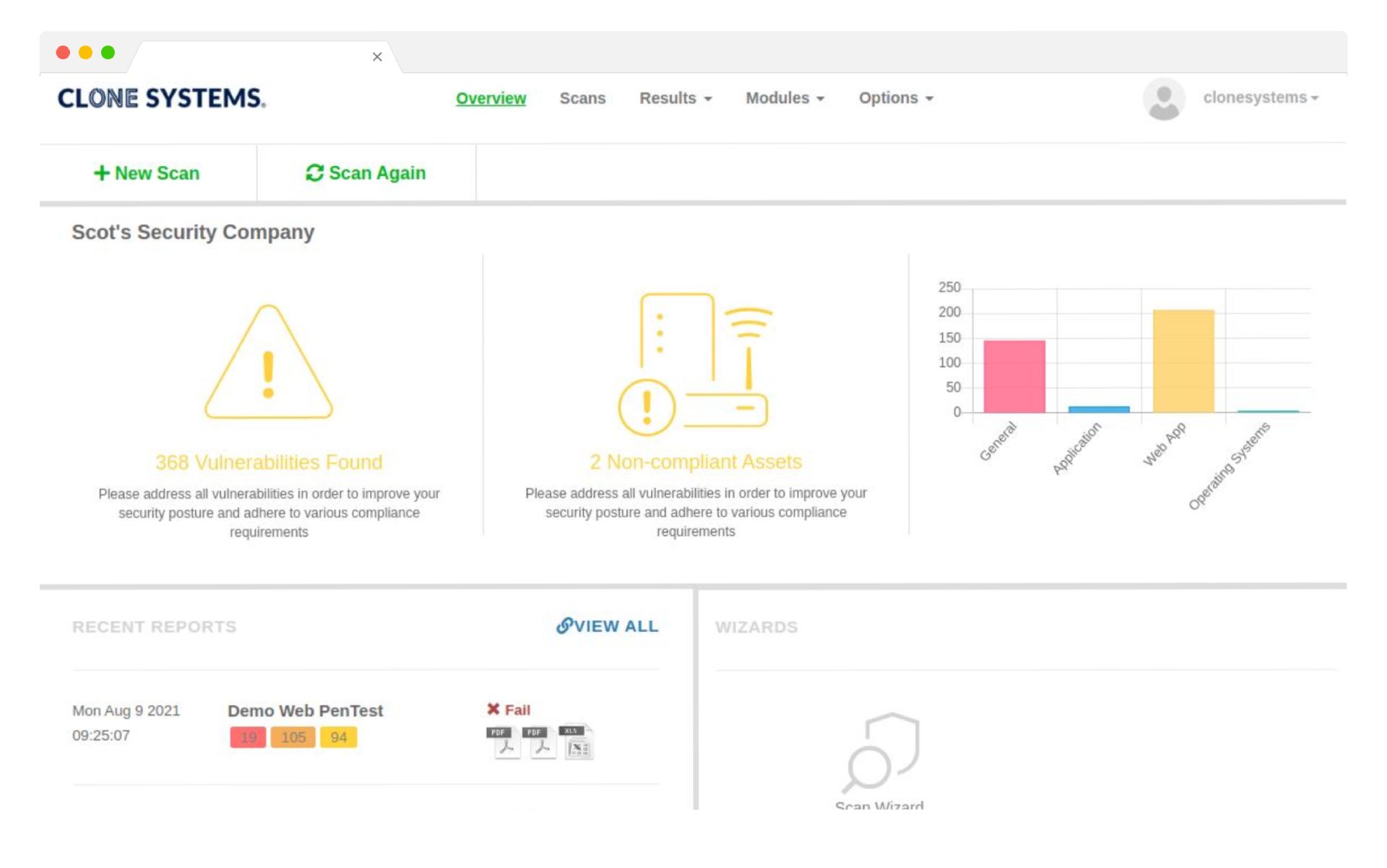
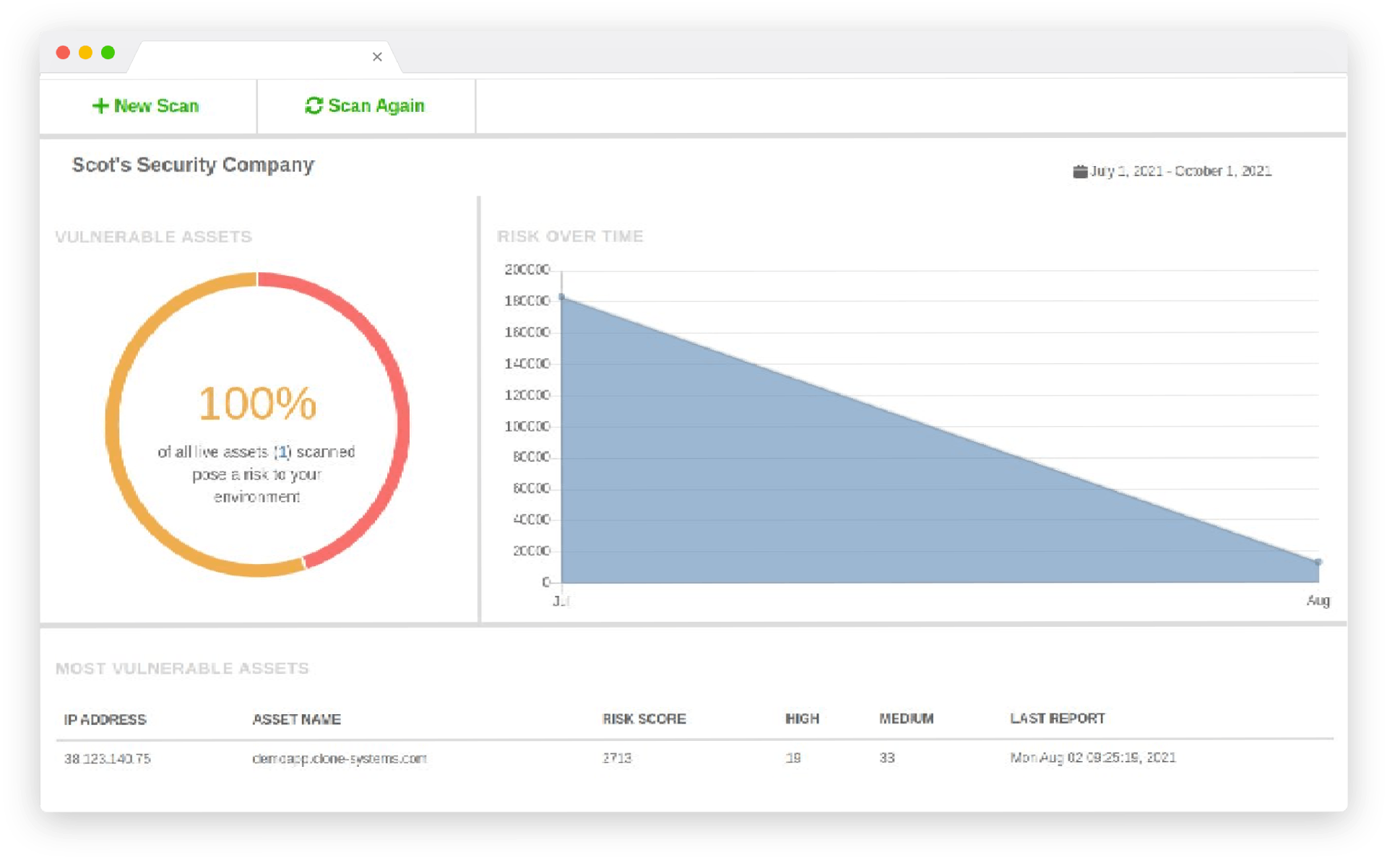
Obtain support, education, and guidance from a certified security engineer on how to improve your network. Our CISSP Engineers have extensive experience assessing security and compliance vulnerabilities. Detailed vulnerability report including high, medium, and low vulnerabilities found and exploited with remediation guidance and recommendations.
Improve your security posture
Improve your overall security posture and your policies and
procedures by understanding the vulnerabilities within your
network and how to remediate them.
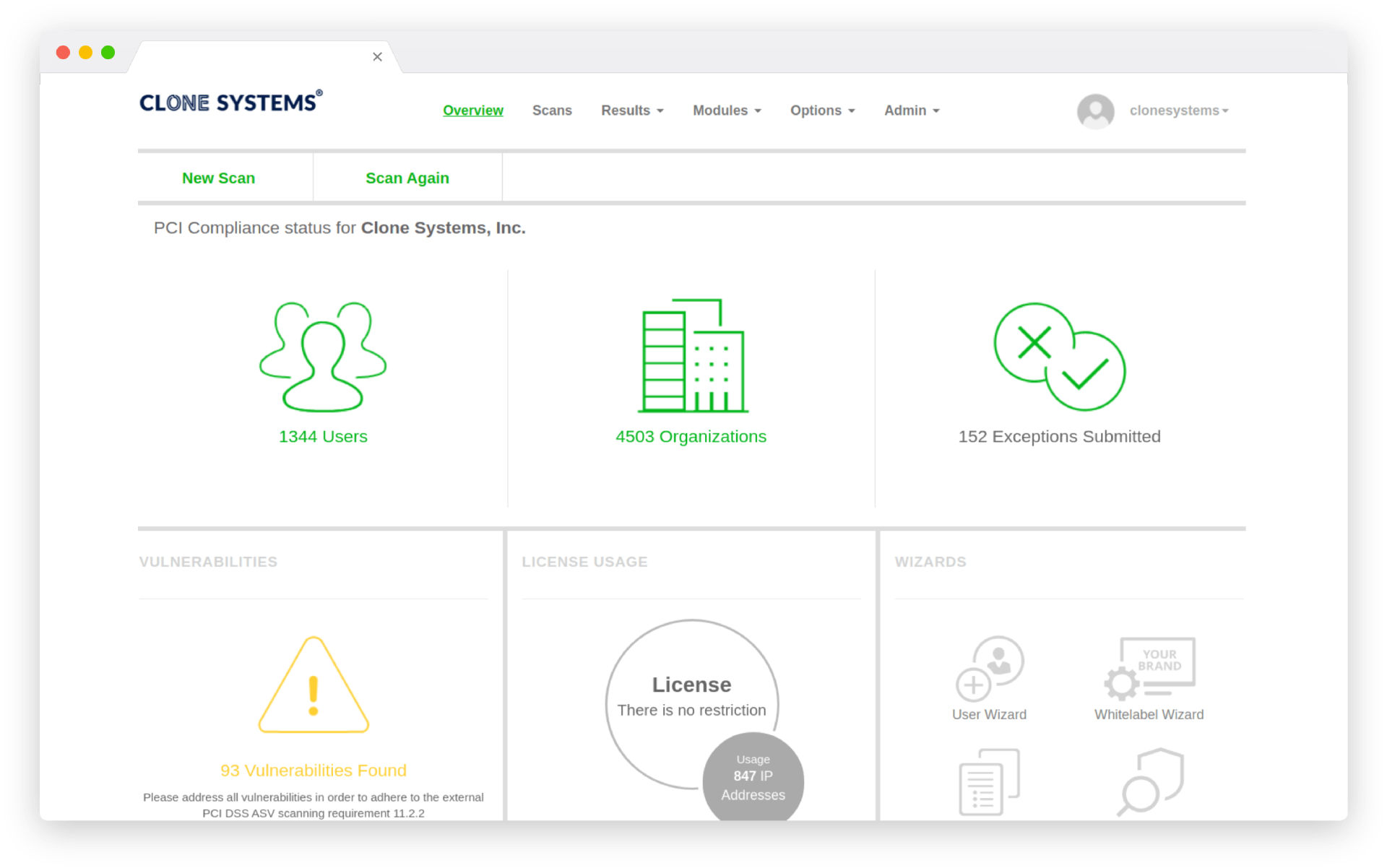
Meet compliance requirements
Meet and exceed audit, regulatory, and compliance requirements validated by Clone Systems security expertise. Receive a certified pass report after assessing that your environment has no high or medium vulnerabilities.
*OnDemand Penetration testing is available if you want your team to conduct the scan.
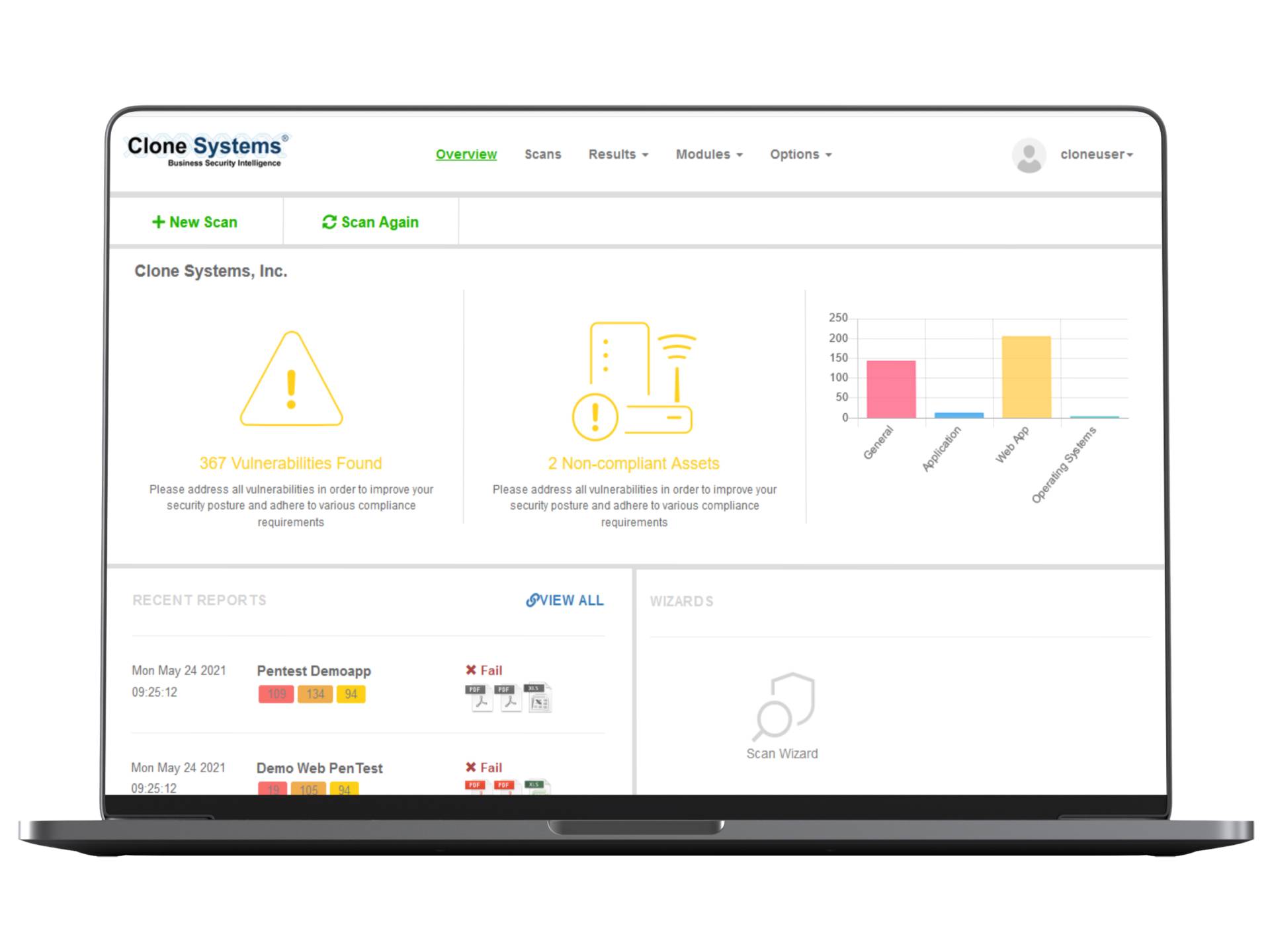
Obtain support and guidance
Obtain support, education, and guidance from a certified security engineer on how to improve your network. Our CISSP Engineers have extensive experience assessing security and compliance vulnerabilities. Detailed vulnerability report including high, medium, and low vulnerabilities found and exploited with remediation guidance and recommendations.
Improve your security posture
Improve your overall security posture and your policies and procedures by understanding the vulnerabilities within your network and how to remediate them.
Meet compliance requirements
Meet and exceed audit, regulatory, and compliance requirements validated by Clone Systems security expertise. Receive a certified pass report after assessing that your environment has no high or medium vulnerabilities.
*OnDemand Penetration testing is available if you want your team to conduct the scan.
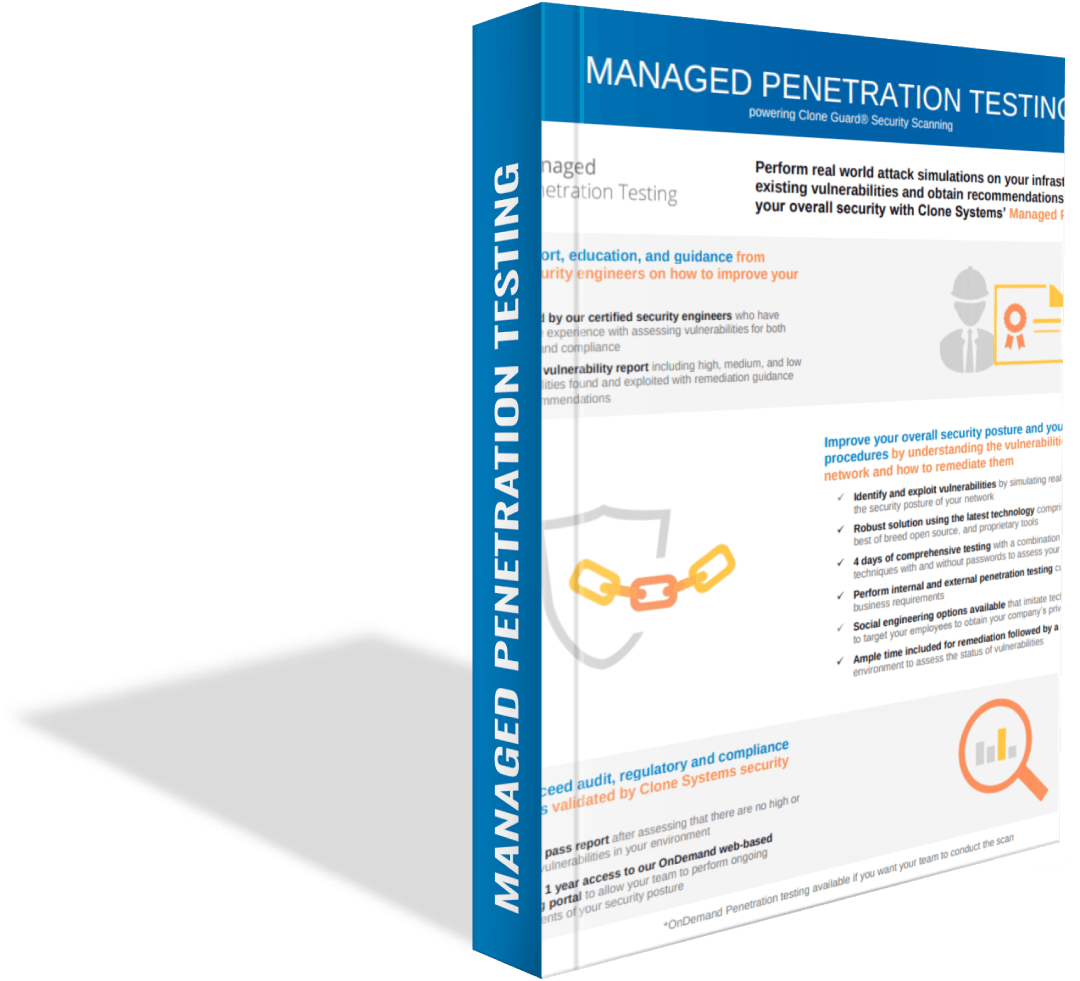
Product Sheet
Discover how you can improve your security posture with the Clone Guard Managed Penetration Testing Product Sheet.