Website Vulnerability Scanning Protect Against Web Attacks and Malware
Reviews
Secure your website from all external threats while achieving compliance.
Website Vulnerability Scanning Protect Against Web Attacks and Malware
Secure your website from all external threats while achieving compliance.
Customers Around the World
Problem & Solution
Protect Your Online Presence
Websites and web applications are prime targets for cybercriminals. Exploiting unpatched plug‑ins, misconfigured servers or insecure code can lead to data breaches, defacements and loss of customer trust.
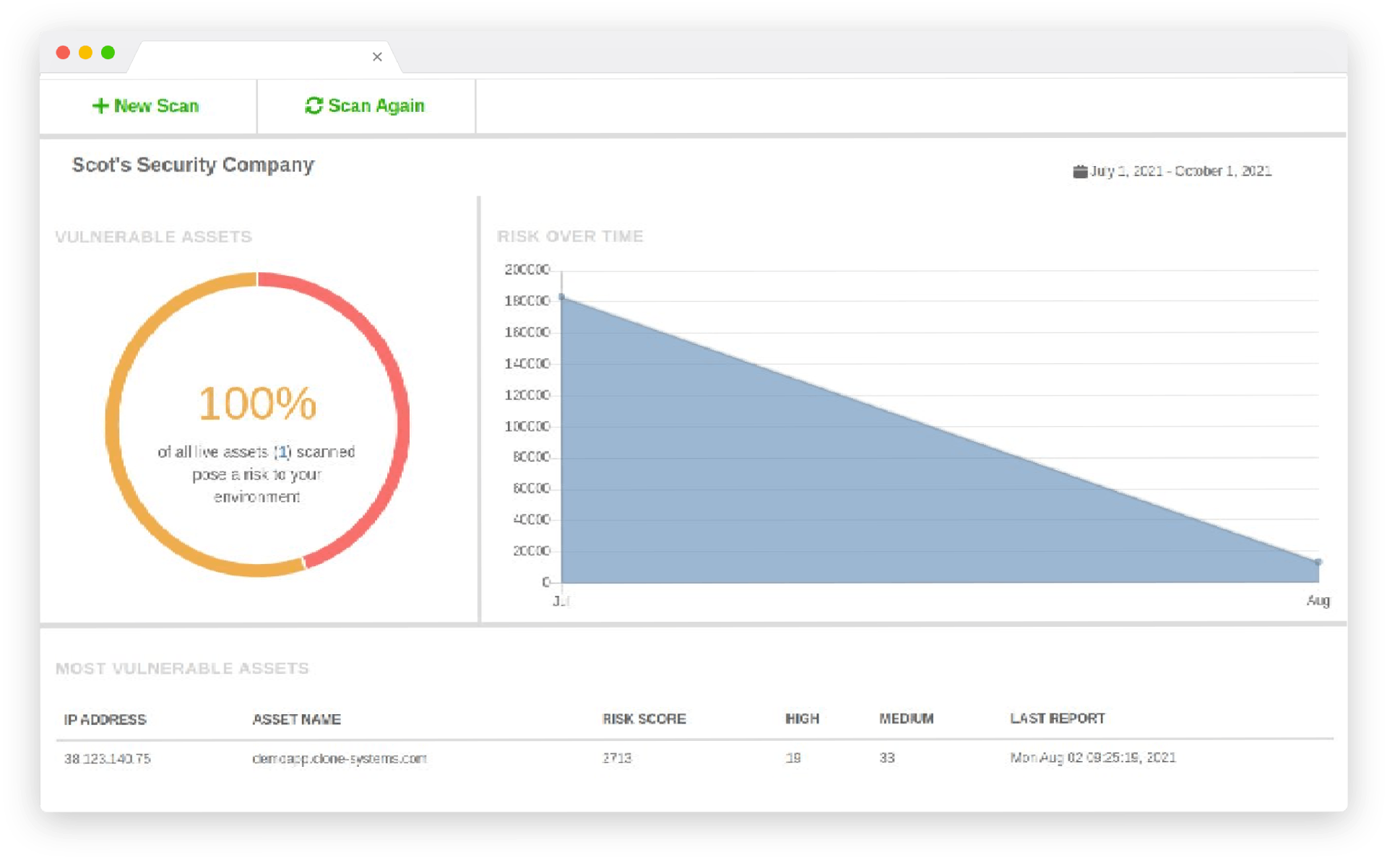
Regular Scanning Keeps You One Step Ahead
Our Website Security Scanning service automatically scans your site for vulnerabilities in content management systems, plug‑ins and custom code. Frequent scans help you detect issues early, maintain compliance and preserve your reputation.
Key Features of Website Vulnerability Scanning
Benefits
Key benefits include:
- Prevent Data Breaches: Identify and fix weaknesses before attackers exploit them.
- Maintain Customer Trust: Secure websites protect your brand and reassure visitors.
- Meet Compliance Requirements: Regular scans help you meet PCI and other regulatory mandates.
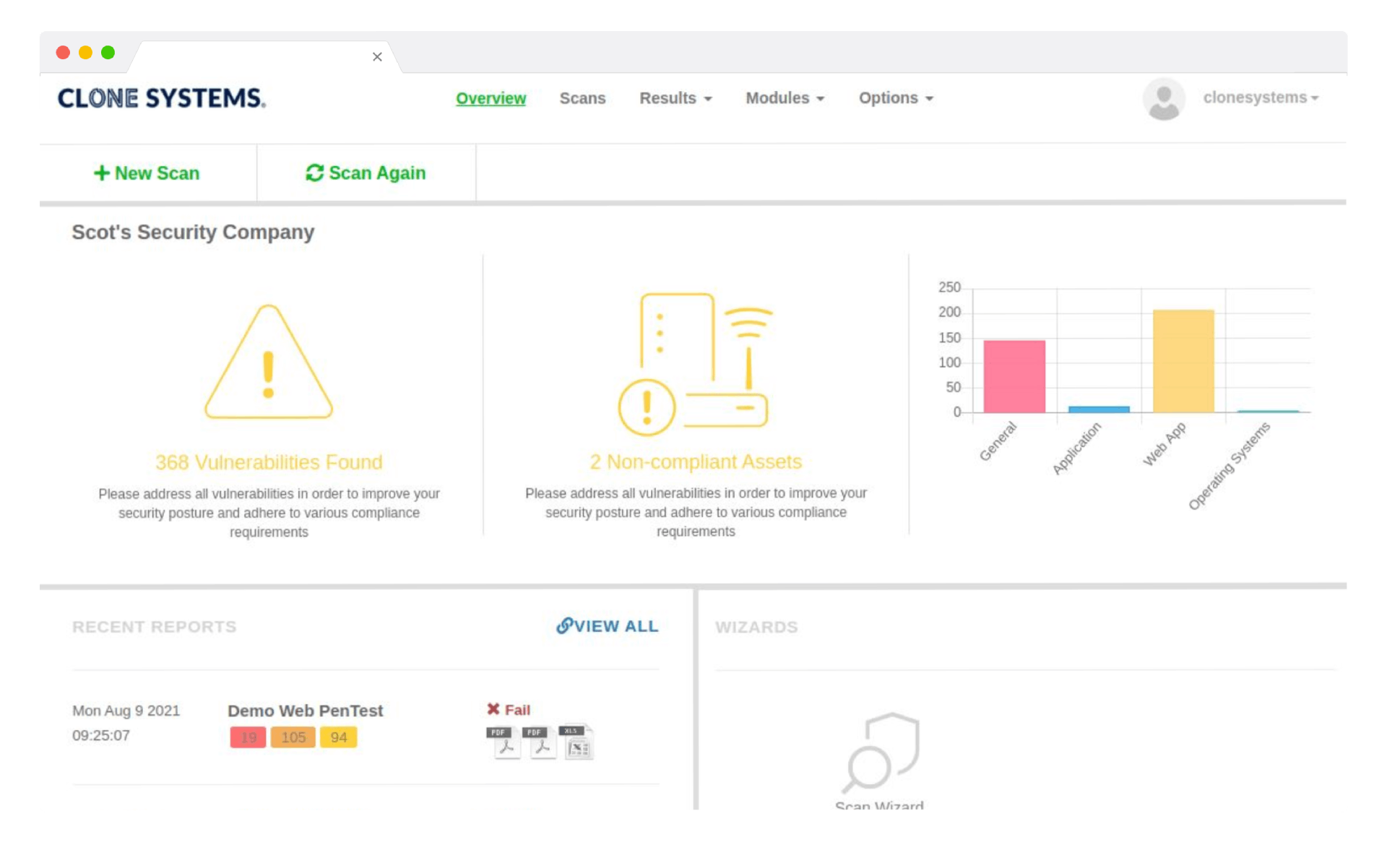
How It Works
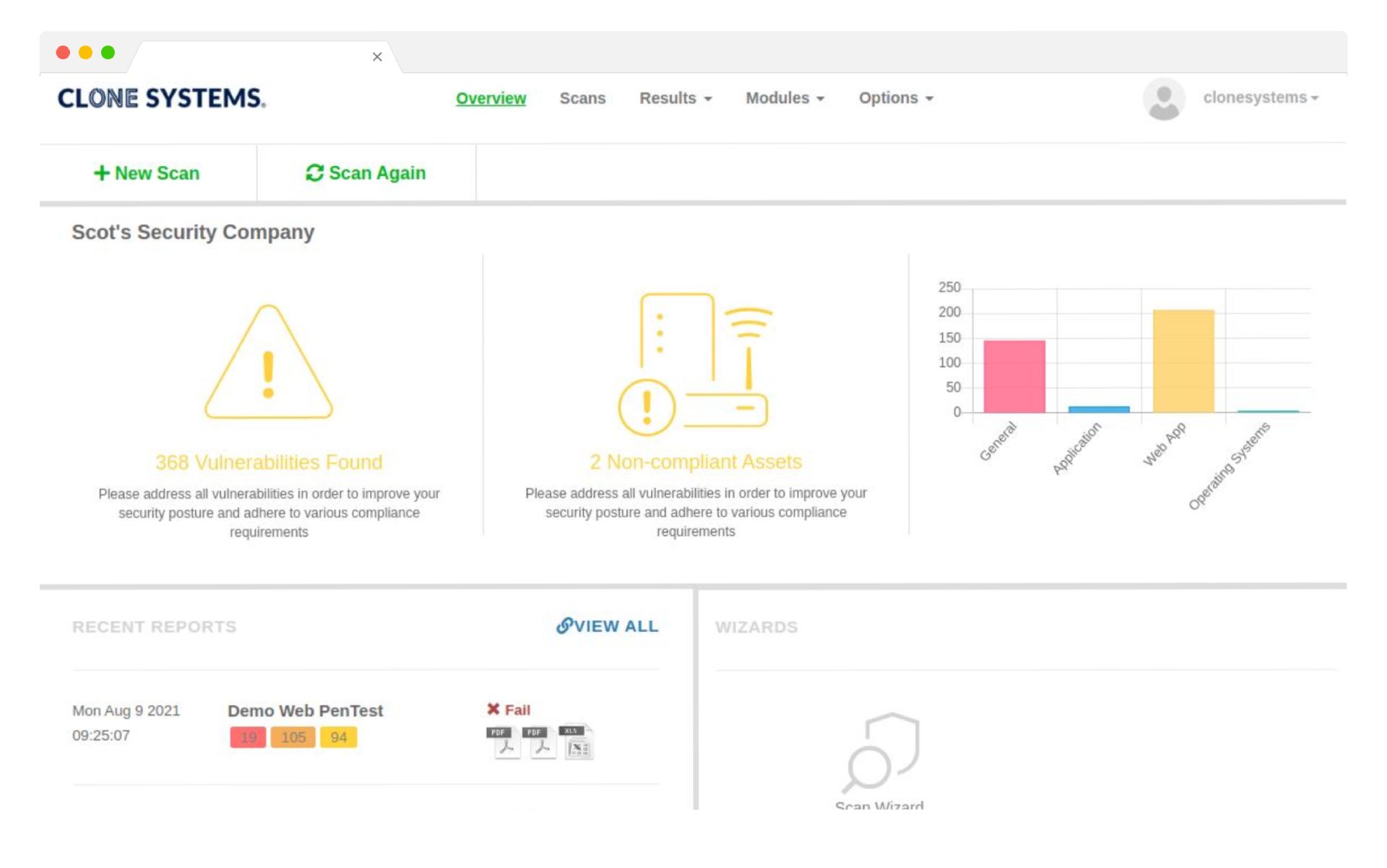
- Schedule or Initiate a Scan: Use our portal to choose a one‑off or recurring scan.
- Automated Testing: The scanner crawls your site, identifies vulnerabilities and tests for common attack vectors.
- Report & Remediate: Receive an easy‑to‑read report with step‑by‑step remediation instructions.
- Monitor Continuously: Set up continuous monitoring to alert you when new vulnerabilities emerge.
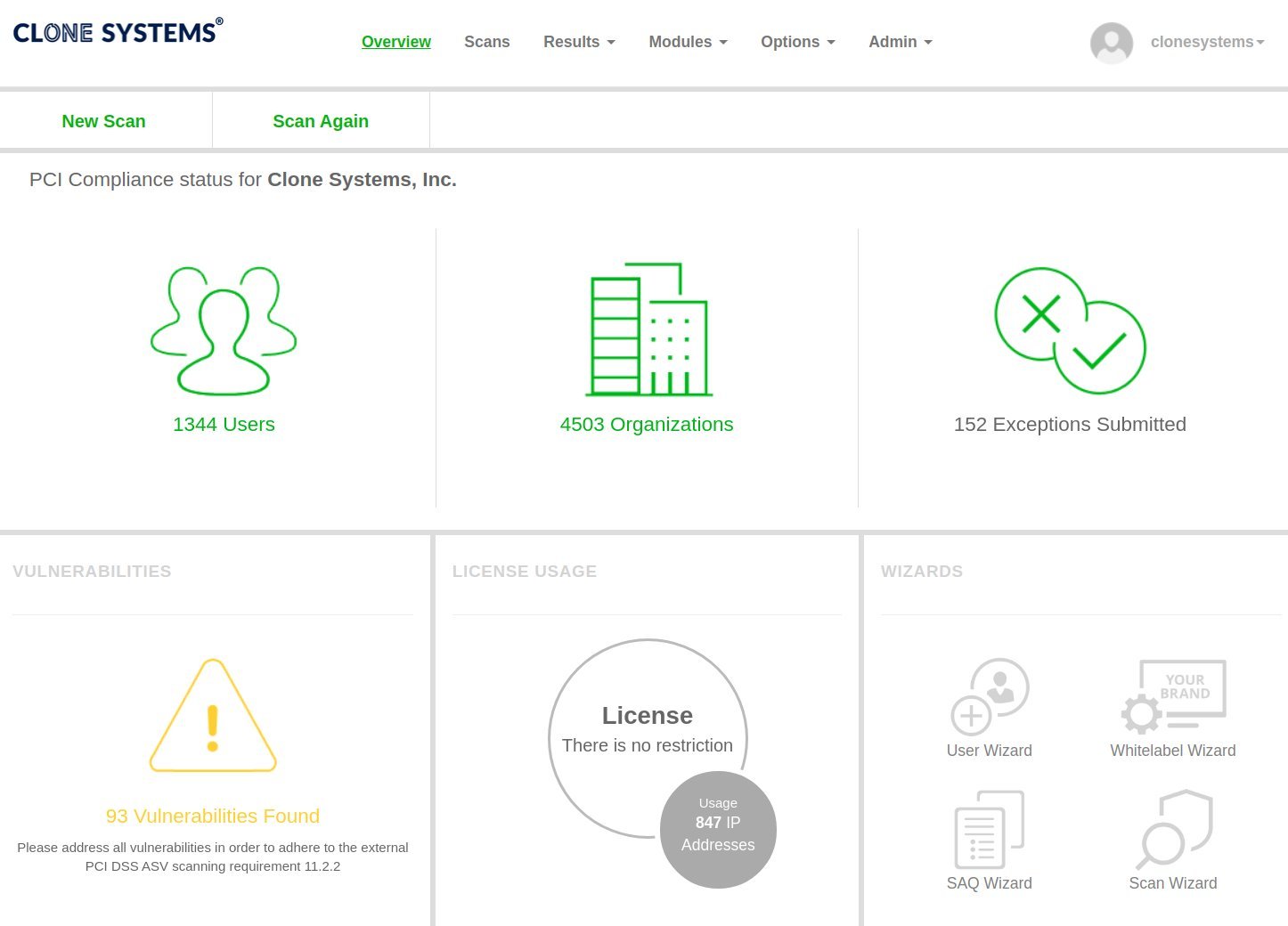
All in one scanning solution for your website
From PCI Scanning to Dark Web Probing, Clone Systems is your one-stop shop for all of your website security scanning needs.
PCI Compliance Scanning
Comply with the PCI DSS standard and safeguard your customer’s data
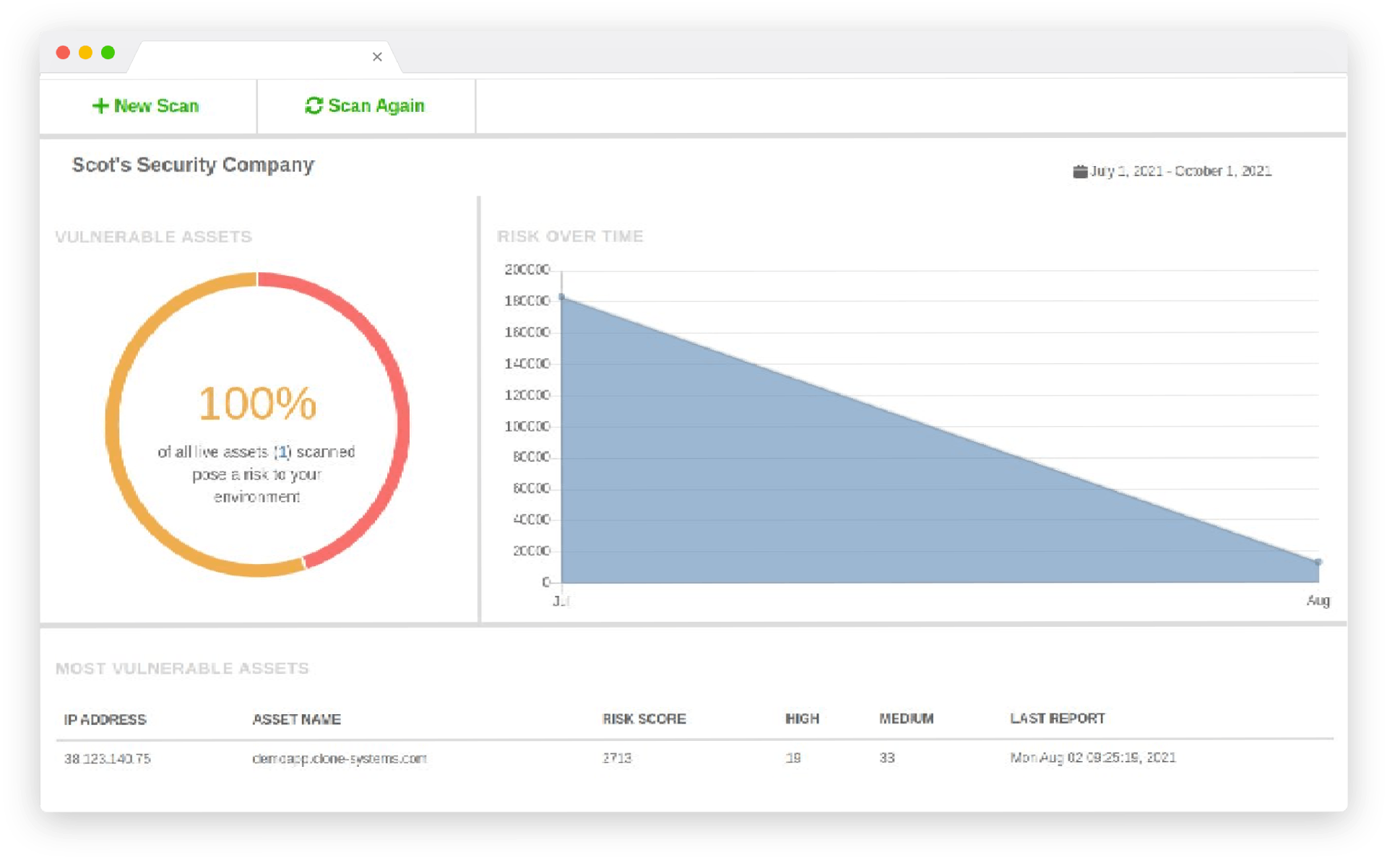
Vulnerability Assessment
Assess the security and integrity of your entire infrastructure

Vulnerability Remedation
Remediate faster and more efficiently with risk prioritization in a multi-vendor environment.
Dark Web Probing
Find Leaked Information and Gain Access to Attack Planning

Website Trust Seal
Increase trust in your website and online business with the Clone Systems Trust Seal
PROTECT your CARDHOLDER DATA
PCI Compliance Scanning
Minimize the risk of compromise for cardholder data and the potential impact on your organization.
Detailed remediation steps for protecting against identified vulnerabilities detected during your PCI security scan. Unlimited re-scans against your website to assess actions taken to fix vulnerabilities. Threat intelligence and signatures are consistently updated from multiple security sources to protect against emerging threats and vulnerabilities.

protect your sensitive data
Dark Web Probing
Detect and recover compromised credentials early in the breach timeframe, before focused account takeover attacks normally start. Infiltrate criminal networks to recover data before it becomes public, allowing businesses to protect sensitive personnel and limit entry points.

Increase your website’s trust
Website Trust Seal
The perception of a safe, verified, and secure website will affect potential customers’ decisions to complete an online purchase. As a result, e-commerce owners gradually realize that to succeed in online retail. They must demonstrate excellent and continuous security validation. Our security website trust seals assure your customers and partners that you care about them.
Evaluate your infrastructure’s security
Vulnerability Assessment
Measure your compliance status against cybersecurity policies and various state and gov laws. Complete trust in the scanning process due to our high-level scanning accuracy. Modern cloud-based scanning technology performs a transparent examination of your website.
improve your overall security
Automated Scripted PenTest
OnDemand web-based portal to conduct self-managed penetration tests against your website. 30-day access for unlimited scanning of your website to assess vulnerabilities for security and compliance. Perform external penetration tests customized to meet your business requirements.
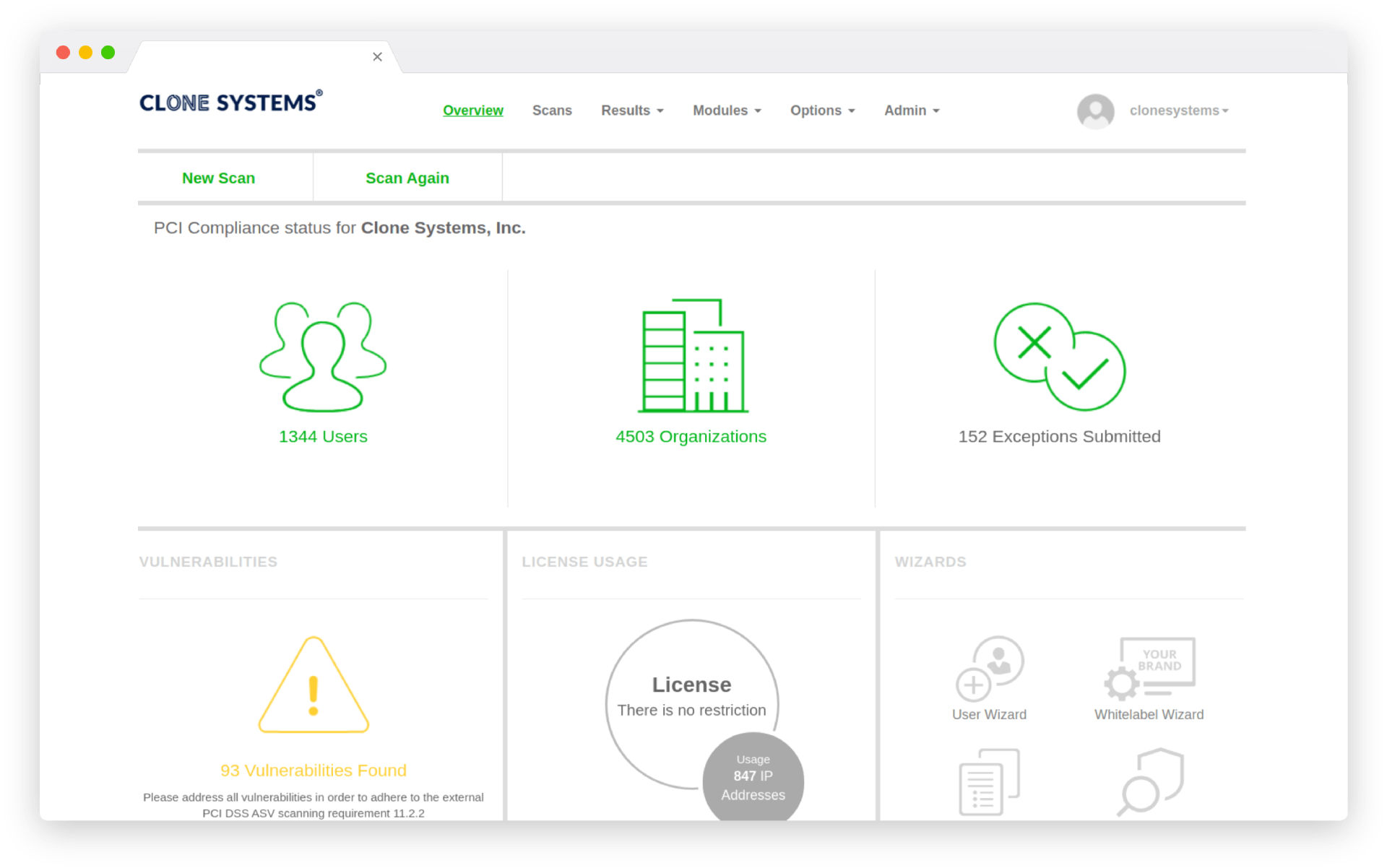
PROTECT YOUR CARDHOLDER DATA
PCI Compliance Scanning
Minimize the risk of compromise for cardholder data and the potential impact on your organization. Detailed remediation steps for protecting against identified vulnerabilities detected during your PCI security scan. Unlimited re-scans against your website to assess actions taken to fix vulnerabilities. Threat intelligence and signatures are consistently updated from multiple security sources to protect against emerging threats and vulnerabilities.
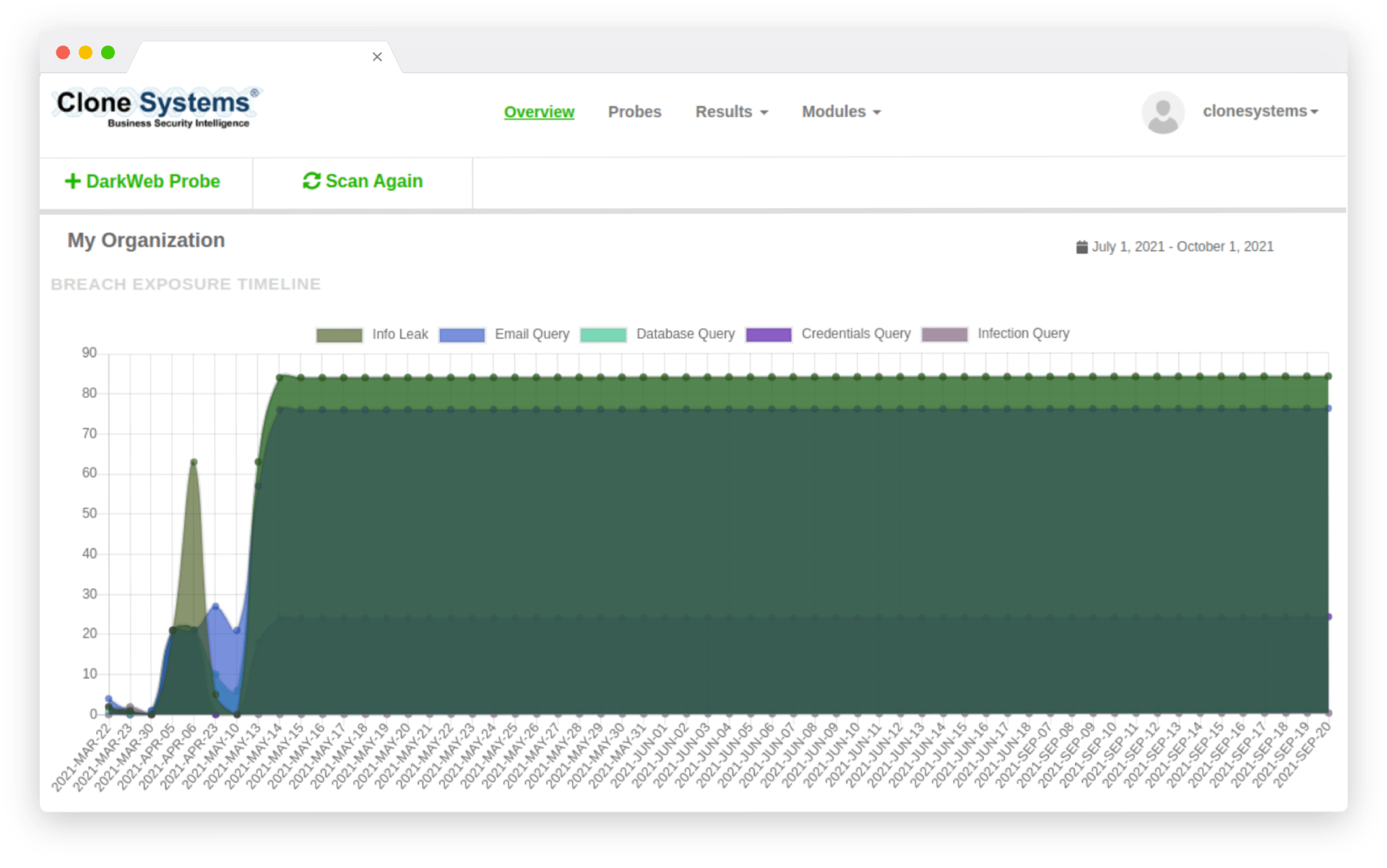
PROTECT YOUR SENSITIVE DATA
Dark Web Probing
Detect and recover compromised credentials early in the breach timeframe, before focused account takeover attacks normally start. Infiltrate criminal networks to recover data before it becomes public, allowing businesses to protect sensitive personnel and limit entry points.
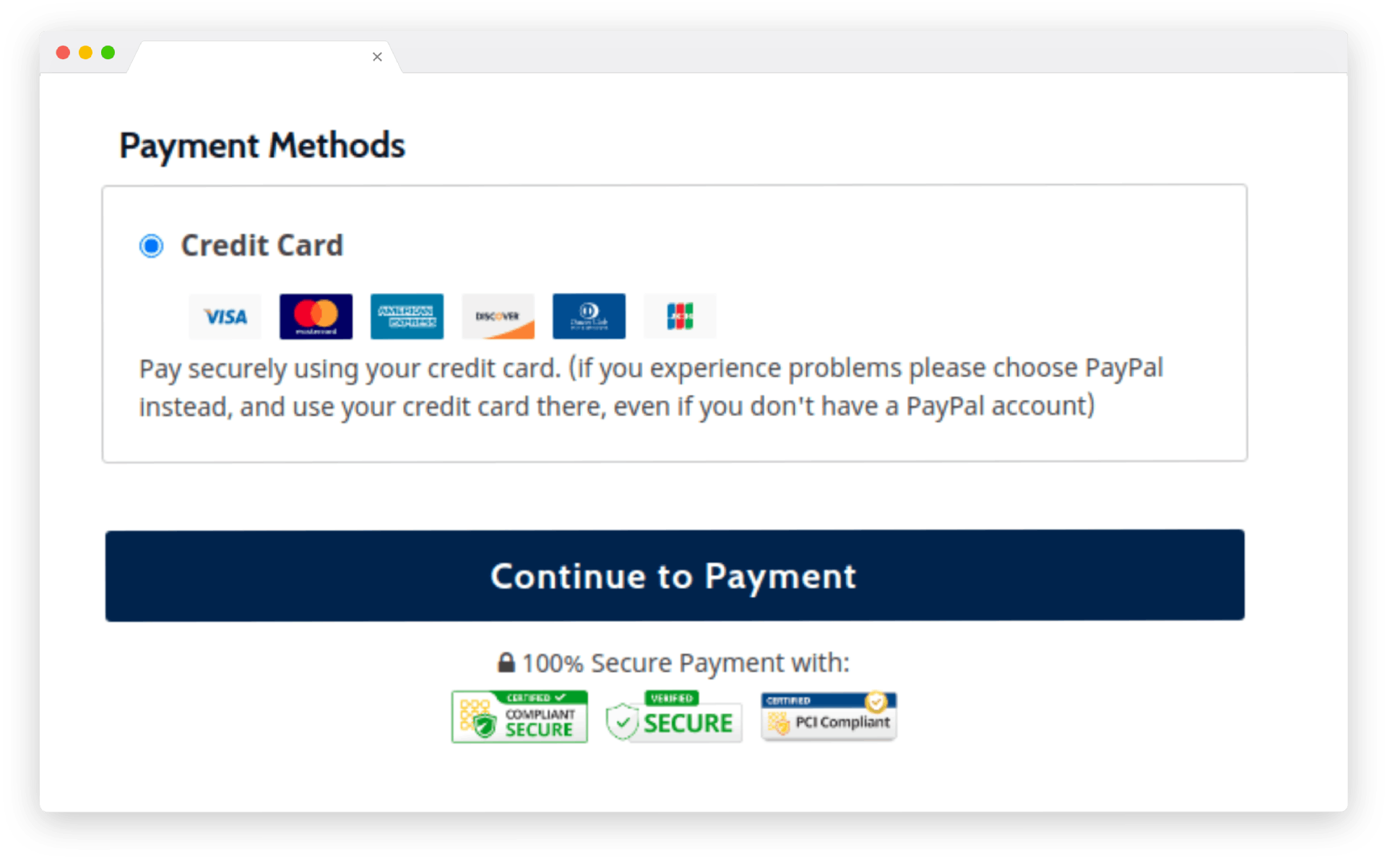
INCREASE YOUR WEBSITE’S TRUST
Website Trust Seal
The perception of a safe, verified, and secure website will affect potential customers’ decisions to complete an online purchase. As a result, e-commerce owners gradually realize that to succeed in online retail. They must demonstrate excellent and continuous security validation. Our security website trust seals assure your customers and partners that you care about them.
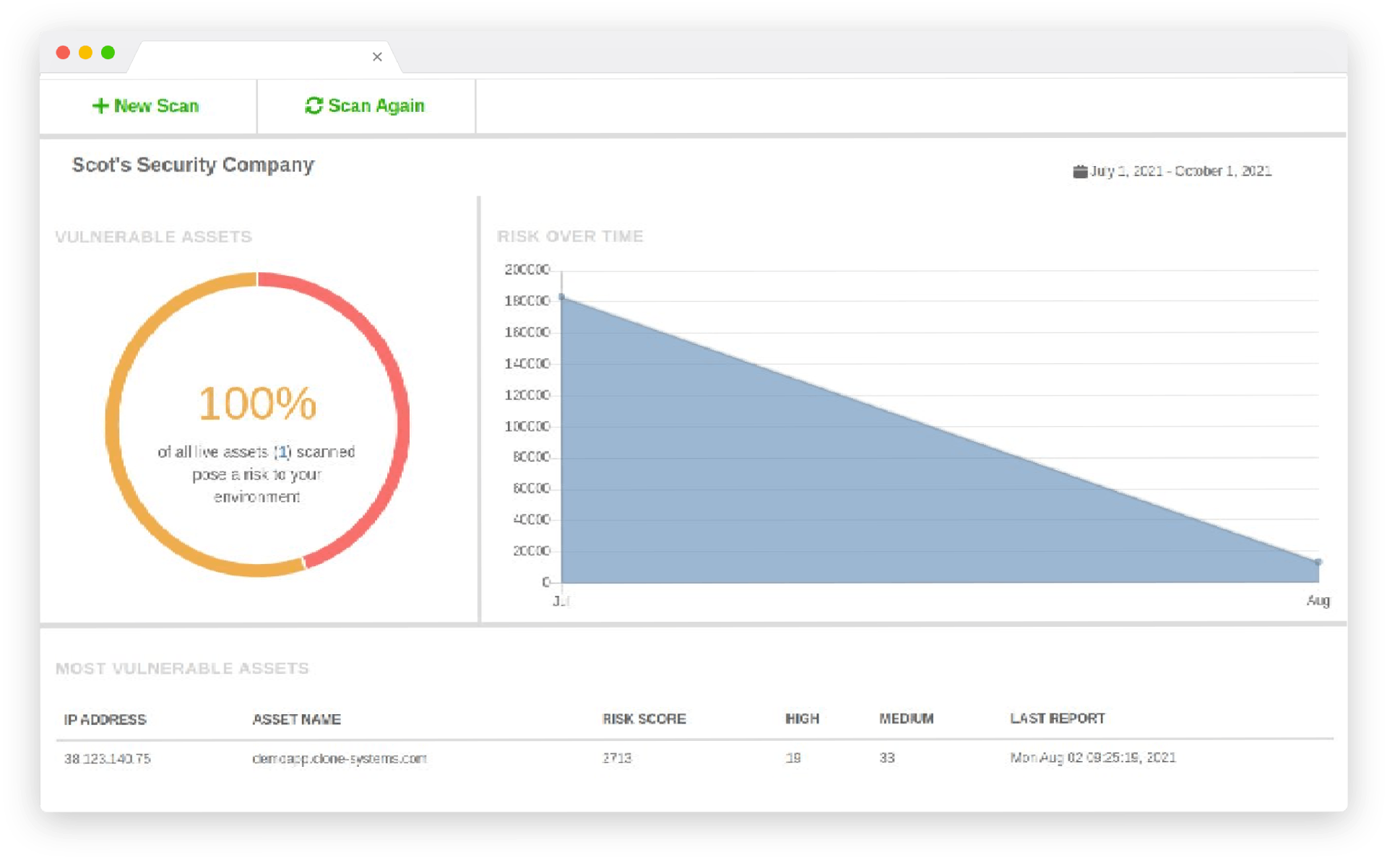
EVALUATE YOUR INFRASTRUCTURE’S SECURITY
Vulnerability Assessment
Measure your compliance status against cybersecurity policies and various state and gov laws. Complete trust in the scanning process due to our high-level scanning accuracy. Modern cloud-based scanning technology performs a transparent examination of your website.
IMPROVE YOUR OVERALL SECURITY
Automated Scripted PenTest
OnDemand web-based portal to conduct self-managed penetration tests against your website. 30-day access for unlimited scanning of your website to assess vulnerabilities for security and compliance. Perform external penetration tests customized to meet your business requirements.
Secure your Website Platform
Compatibility with all Website Platforms and CMS