Customers Around the World
Problem & Solution
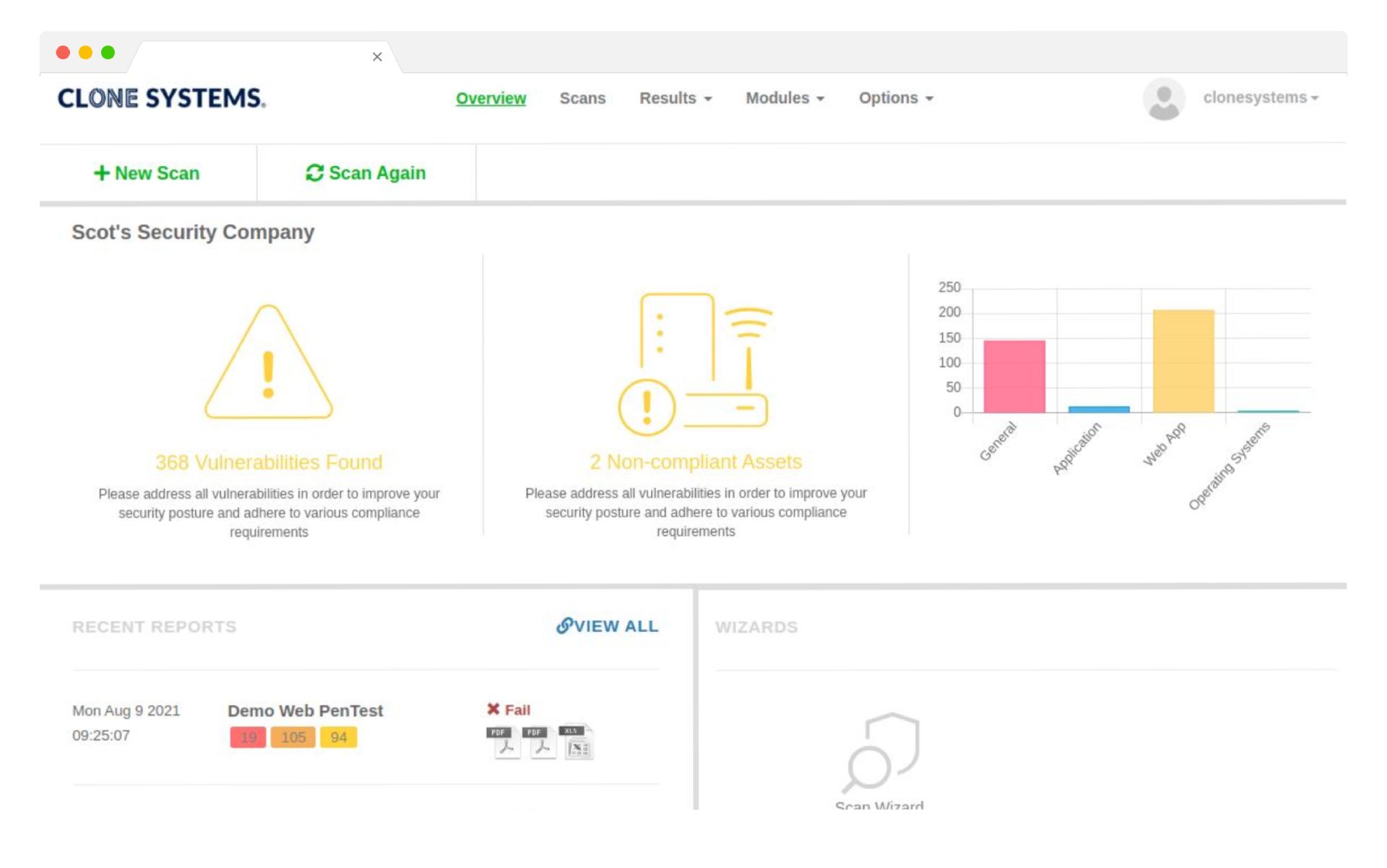
Uncover and Prioritize Your Weaknesses
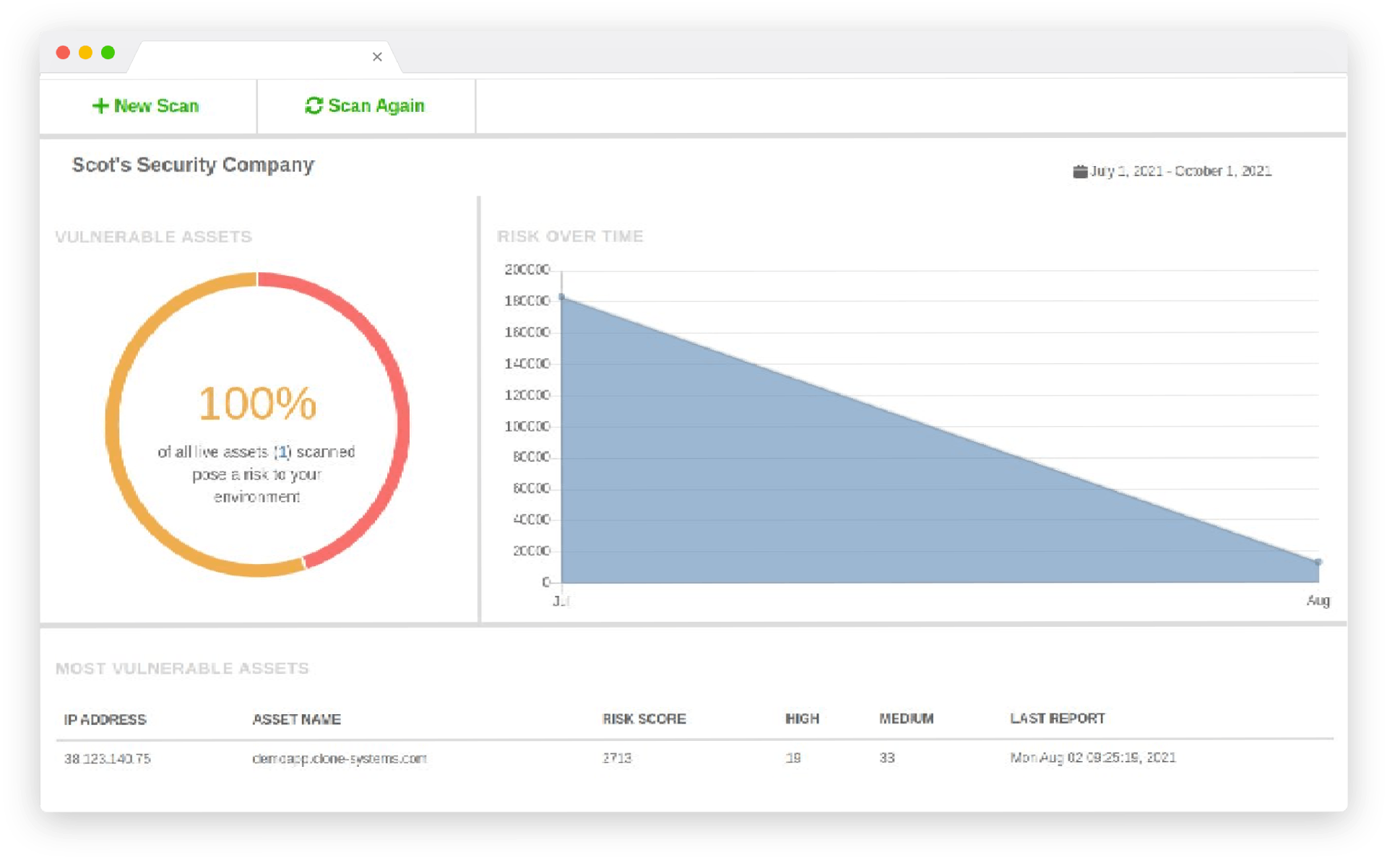
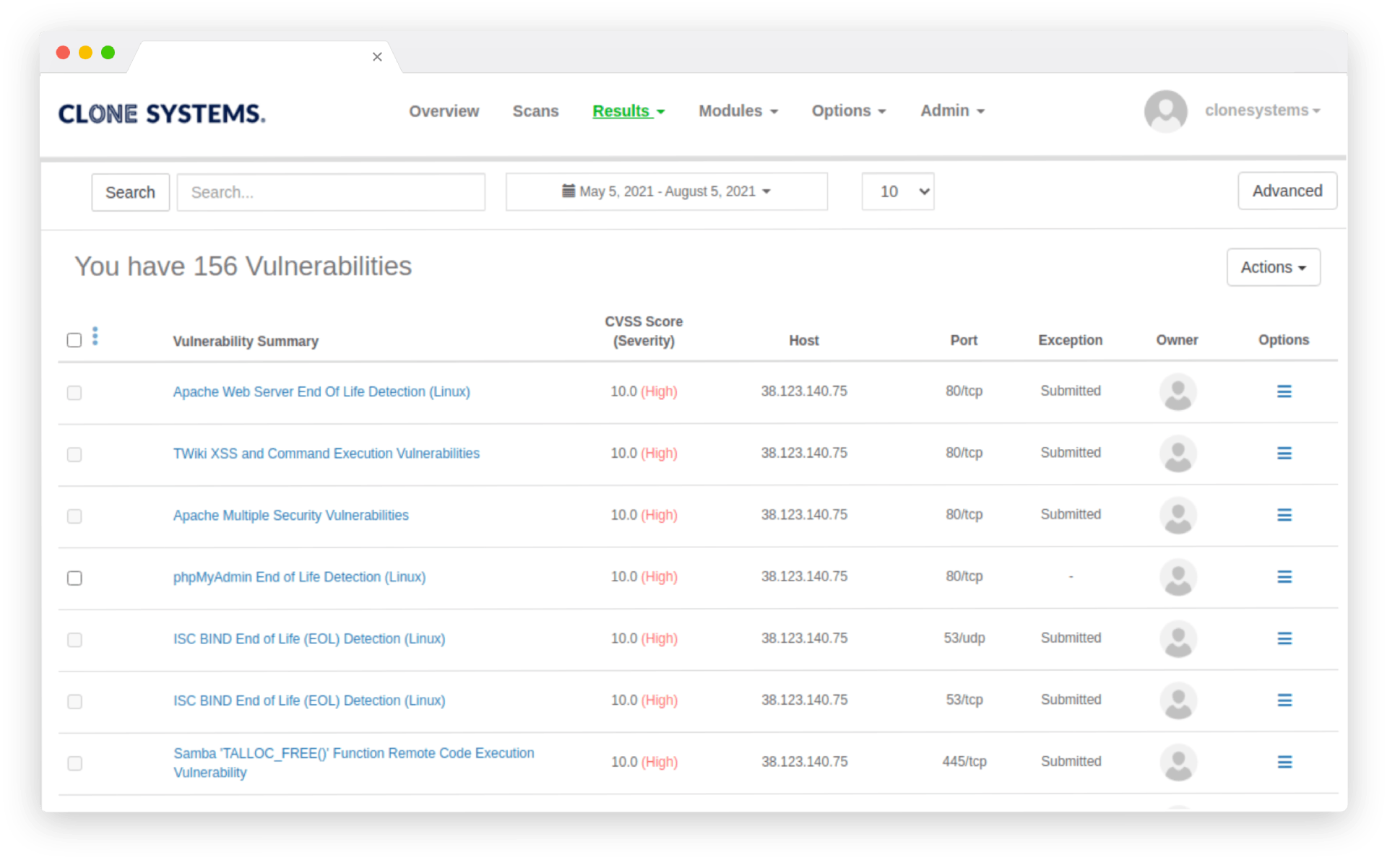
Many organizations lack a clear picture of the assets they own and the vulnerabilities that could lead to compromise. Without insight into missing patches, misconfigurations or outdated software, it’s nearly impossible to defend against attackers.
Comprehensive Assessments for Informed Decisions
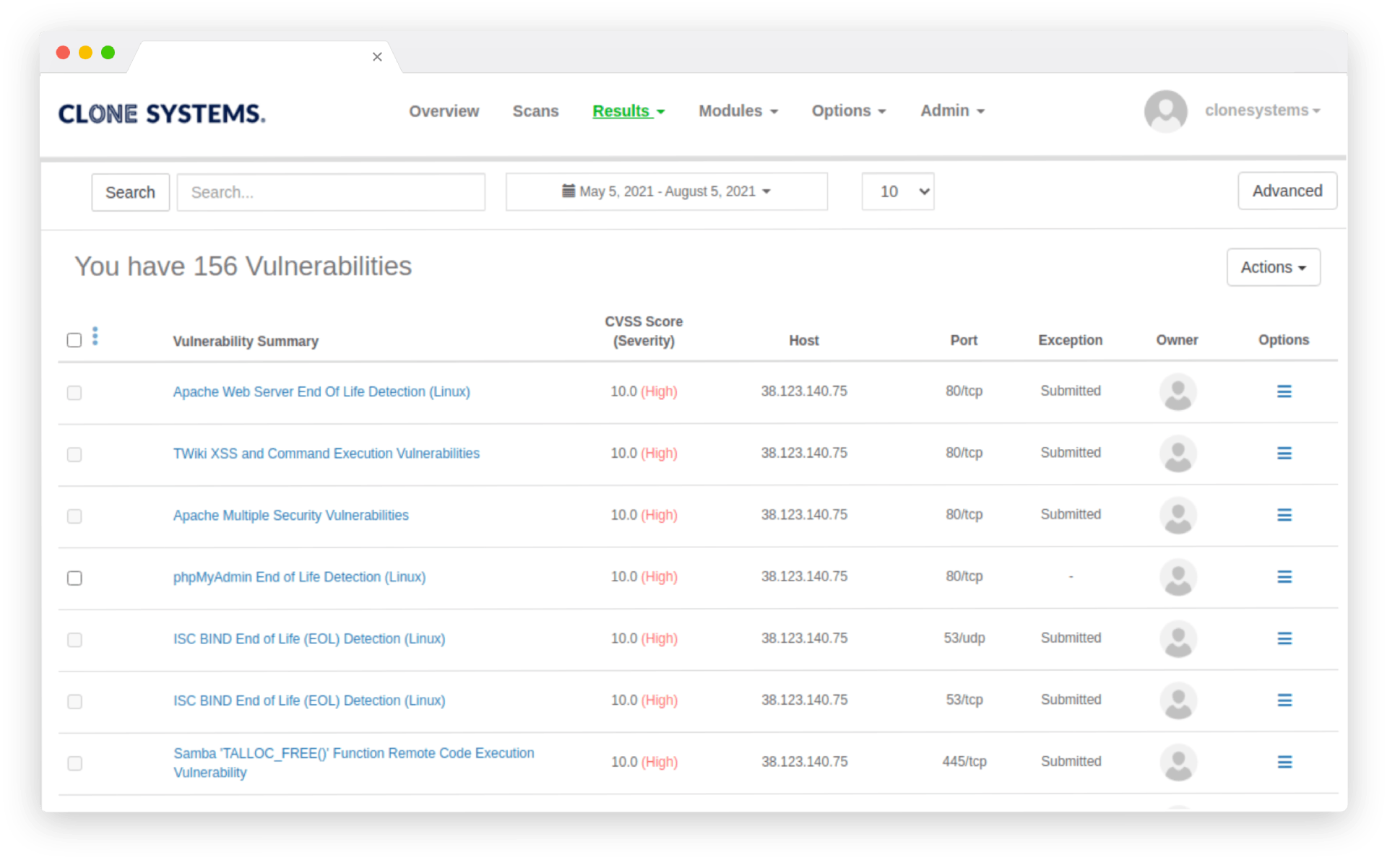
Our Vulnerability Assessment service discovers assets across your network and applications, evaluates their exposure to known vulnerabilities and misconfigurations, and provides prioritized remediation guidance so you can address the most critical issues first.
Key Features of Vulnerability Assessment
Benefits
Choosing a managed SOC isn’t just about convenience—it improves your overall security and business efficiency. Key benefits include:
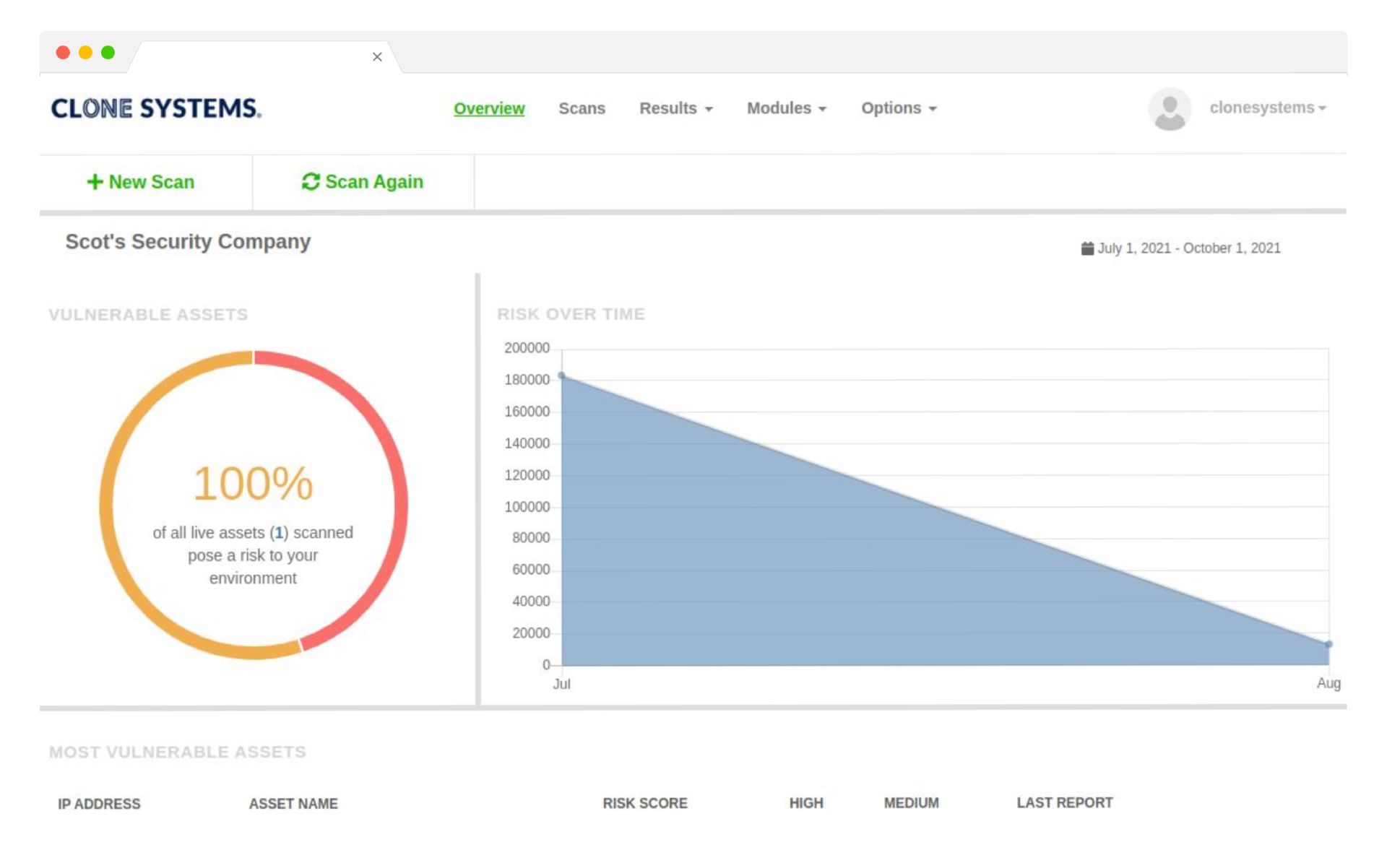
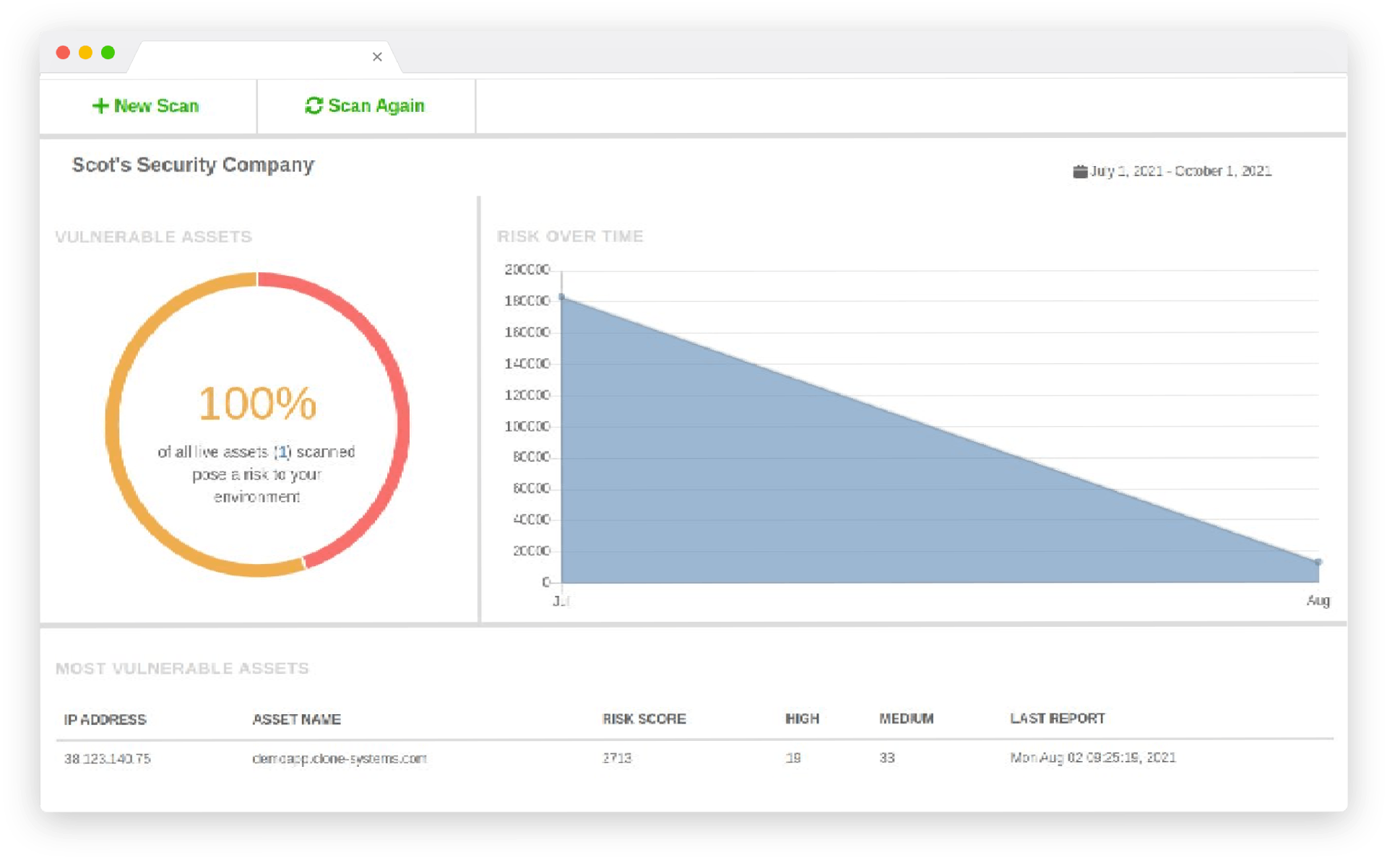
- Improved Visibility: Understand the full scope of your attack surface.
- Better Resource Allocation: Focus remediation efforts on the most critical vulnerabilities and assets.
- Compliance Support: Demonstrate due diligence to auditors and regulators.
- Continuous Improvement: Track your progress over time and measure the effectiveness of security initiatives.
How It Works
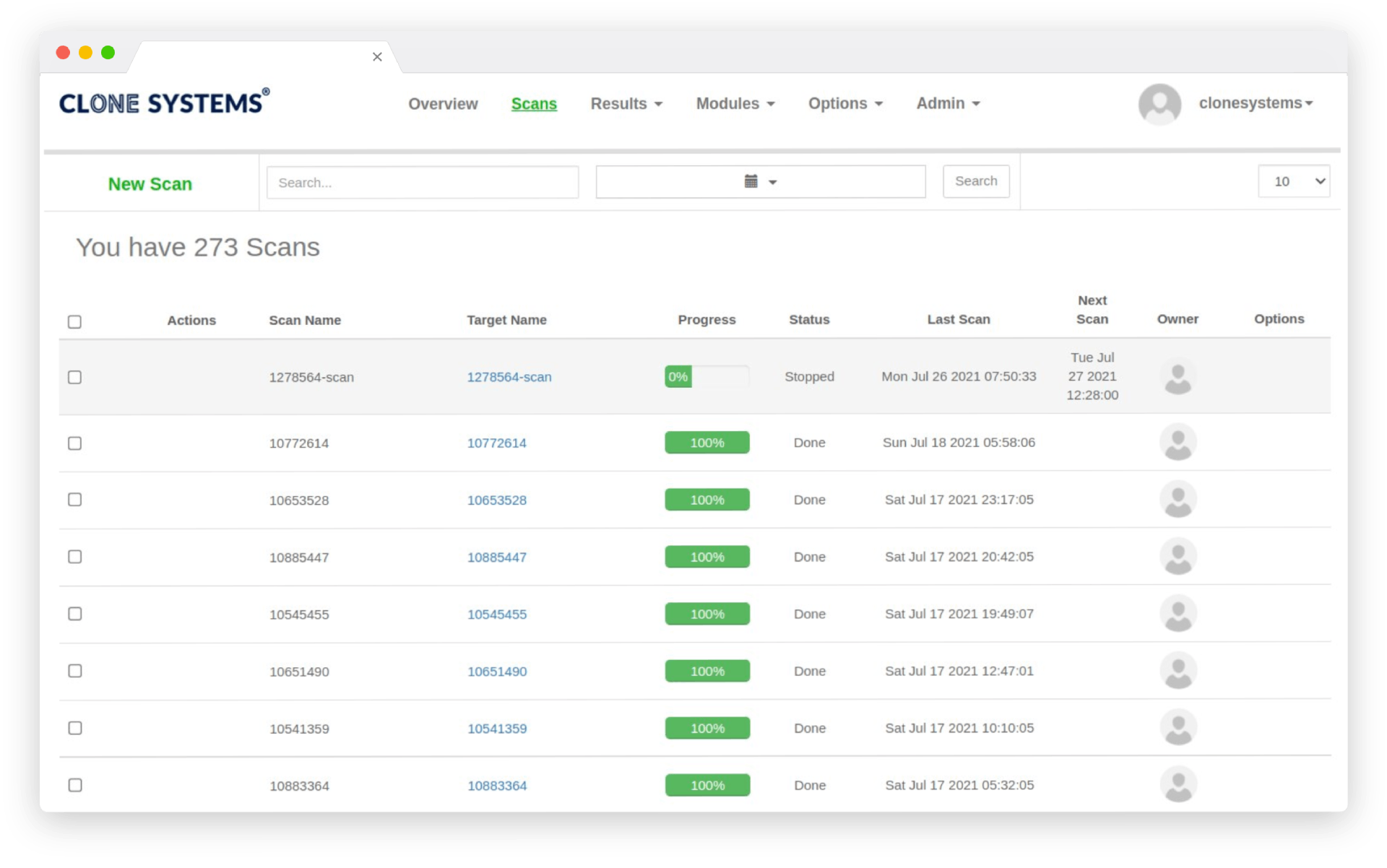
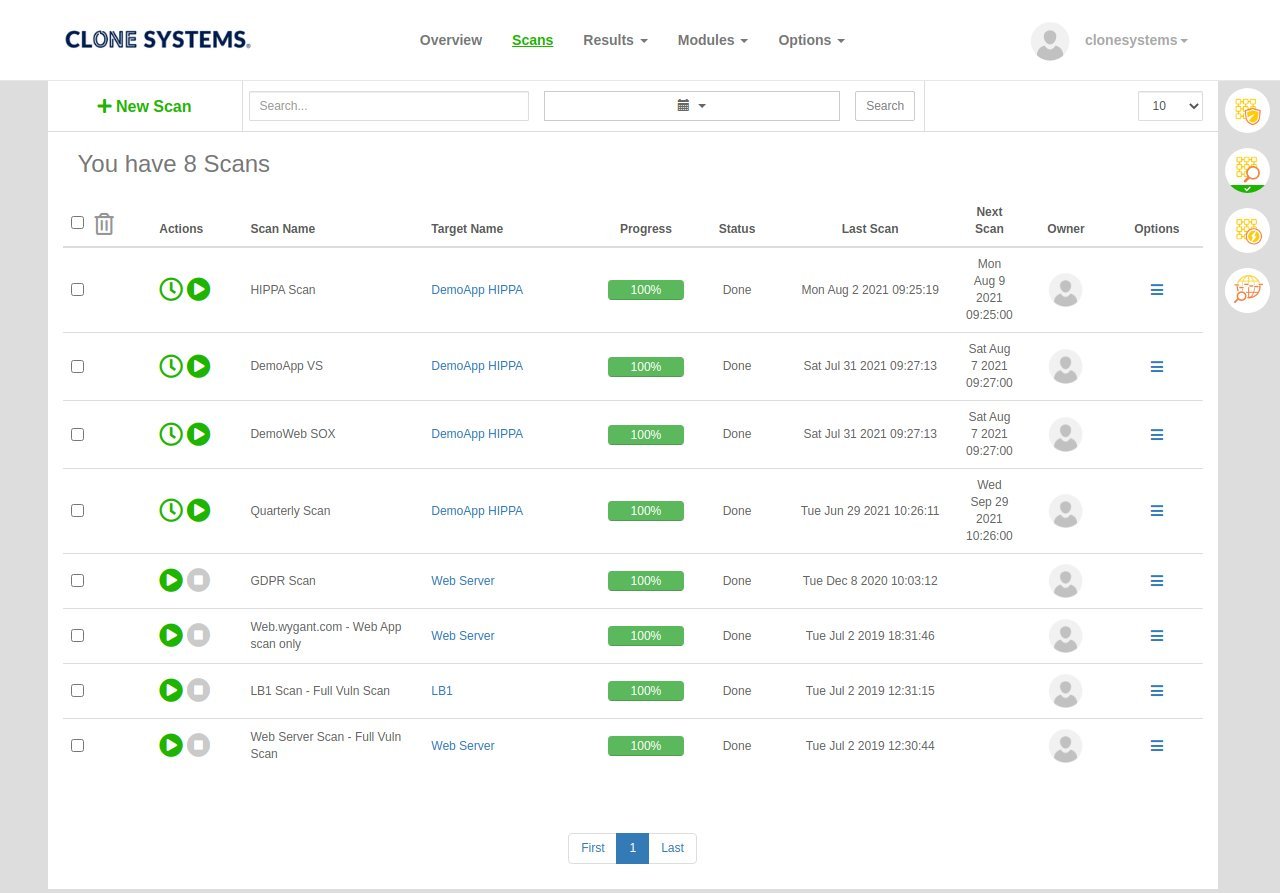
- Discovery: Scan your network to identify all connected devices and services.
- Scanning: Use multiple scanning engines to detect vulnerabilities and misconfigurations.
- Analysis & Prioritization: Assign scores and prioritise findings based on risk and asset value.
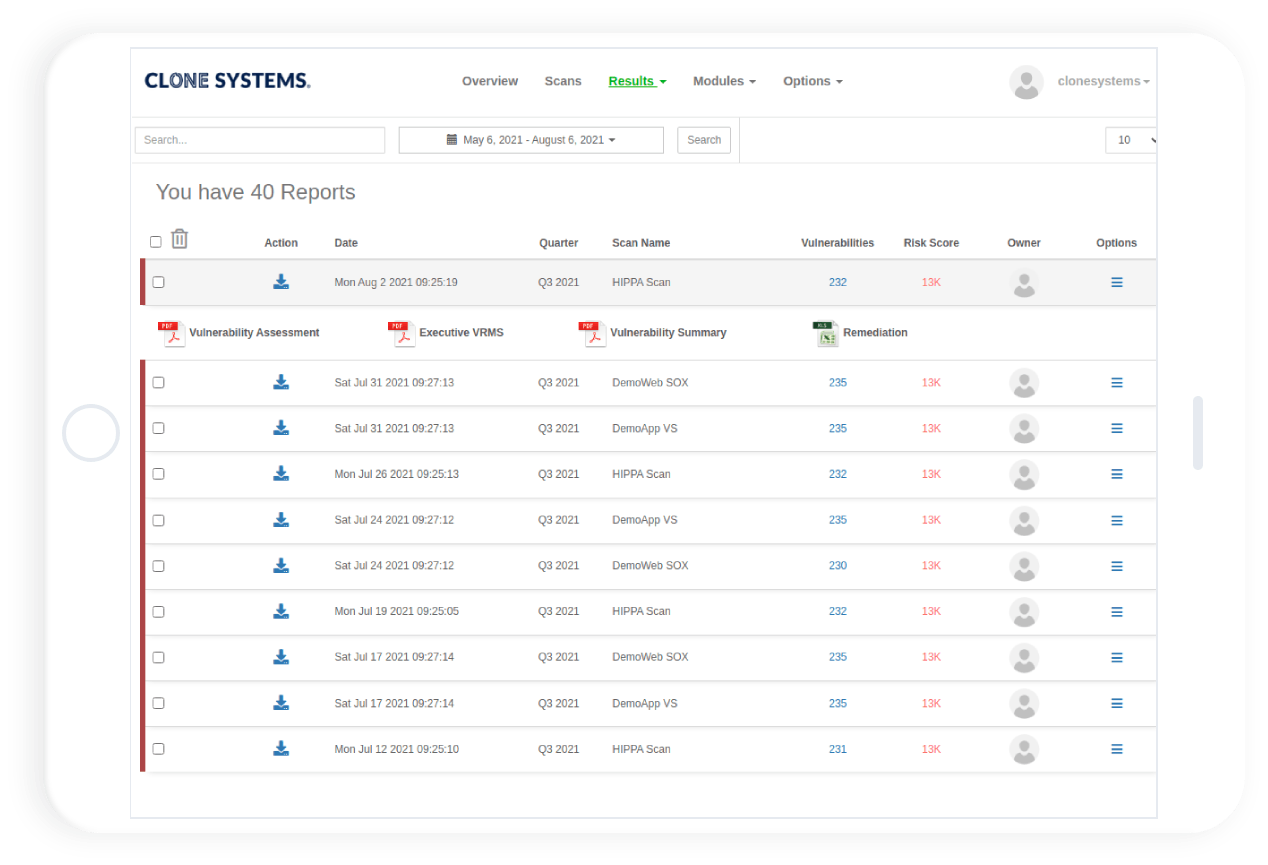
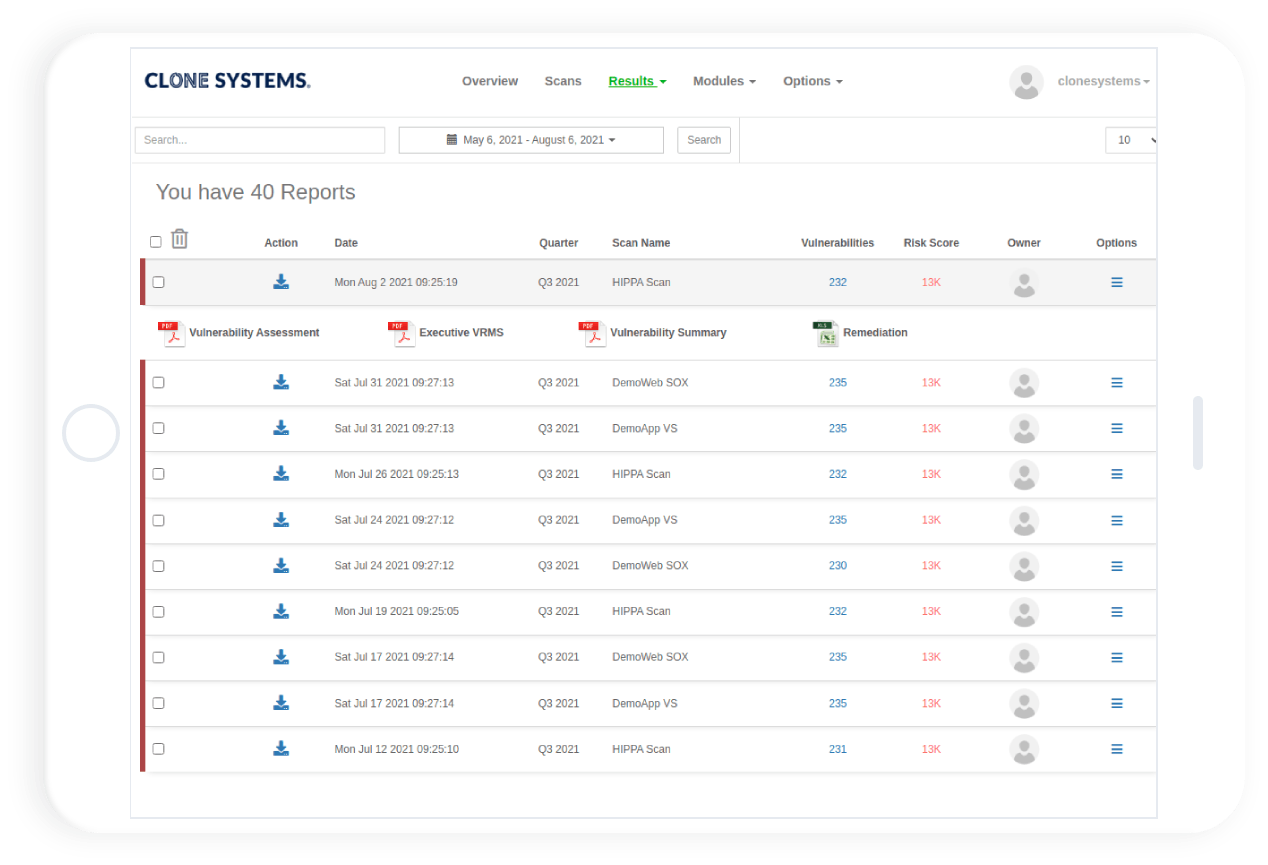
- Reporting: Generate reports with remediation steps, timelines and metrics.
- Rescanning: Conduct follow‑up scans to verify that issues are resolved and track improvements.
Minimize Your Risk
Measure your compliance status against cybersecurity policies and various state and gov laws. Complete trust in the scanning process due to our high-level scanning accuracy. Modern cloud-based scanning technology performs a transparent examination of your network and devices.
Minimize Your Risk
Measure your compliance status against cybersecurity policies and various state and gov laws. Complete trust in the scanning process due to our high-level scanning accuracy. Modern cloud-based scanning technology performs a transparent examination of your network and devices.
External Vulnerability Scanning
Cloud-based scanners continually evaluate the perimeter of your environment. Public, internet-facing vulnerabilities and weaknesses are identified and reported. No software installation or deployment required
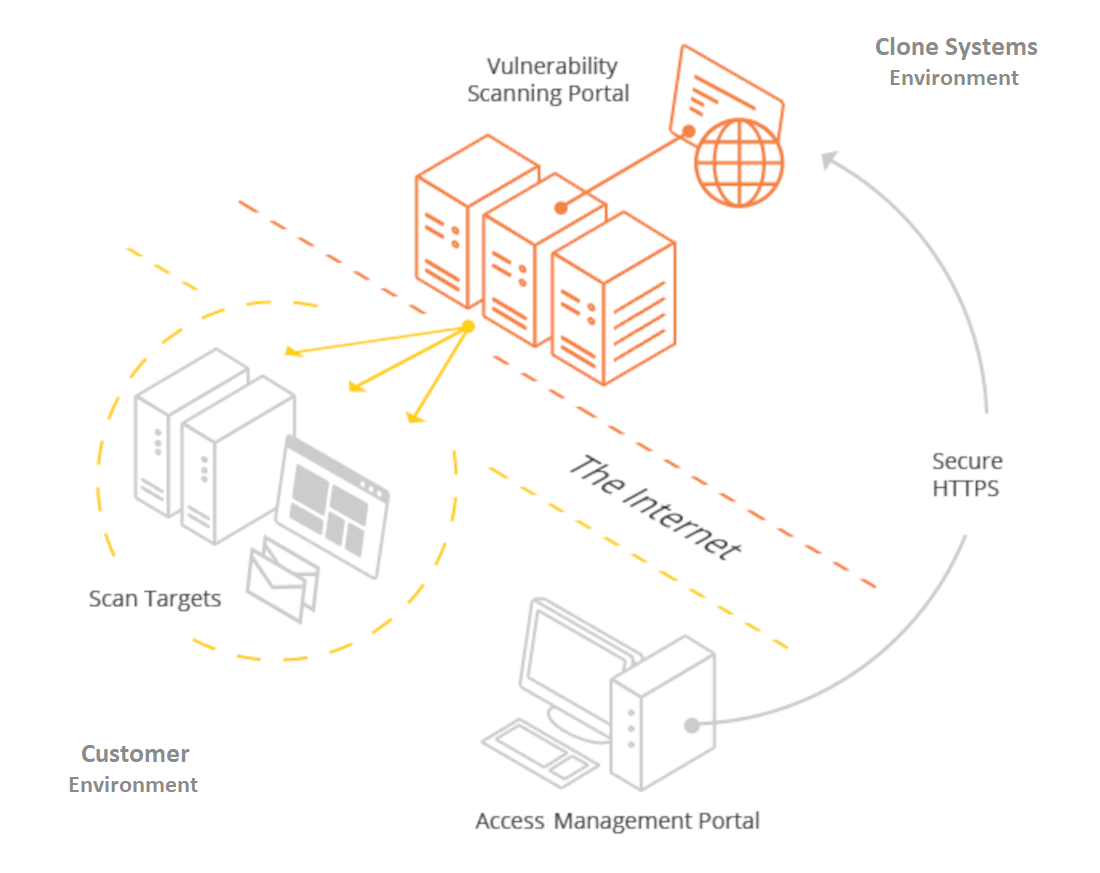
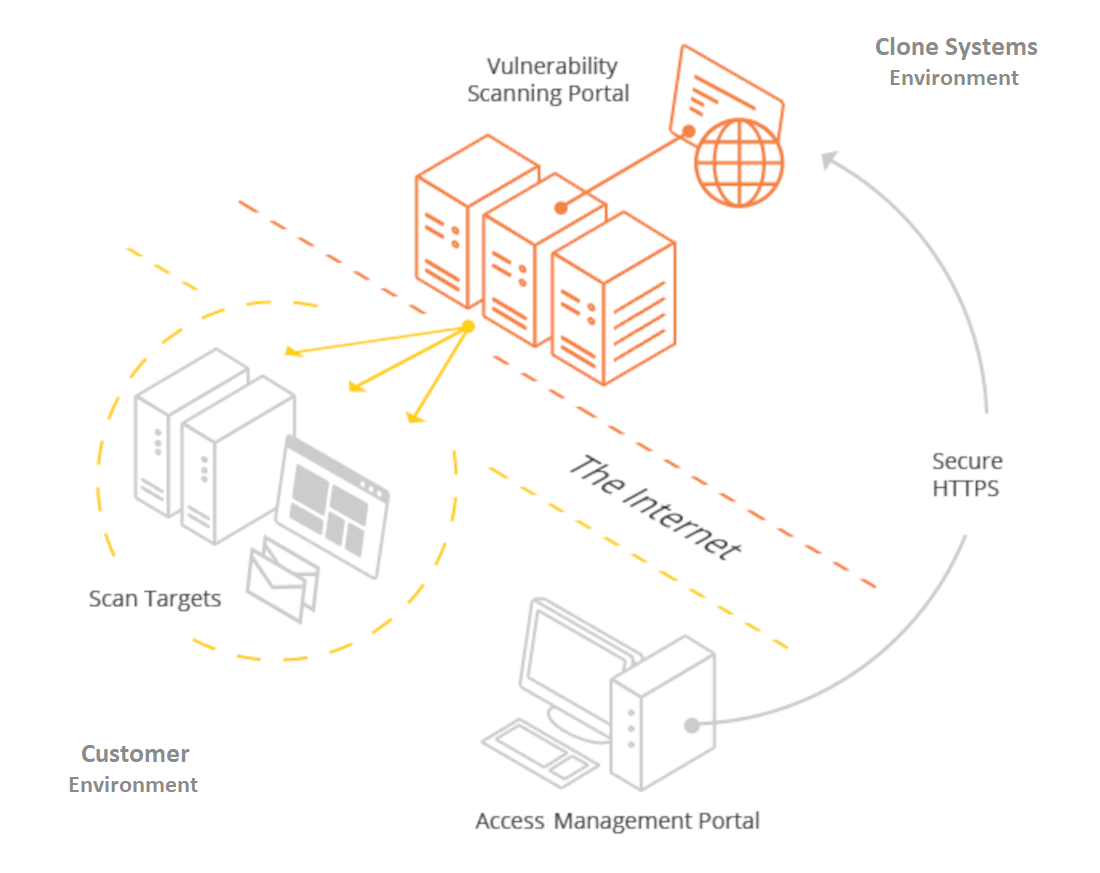
External Vulnerability Scanning
Cloud-based scanners continually evaluate the perimeter of your environment. Public, internet-facing vulnerabilities and weaknesses are identified and reported. No software installation or deployment required.
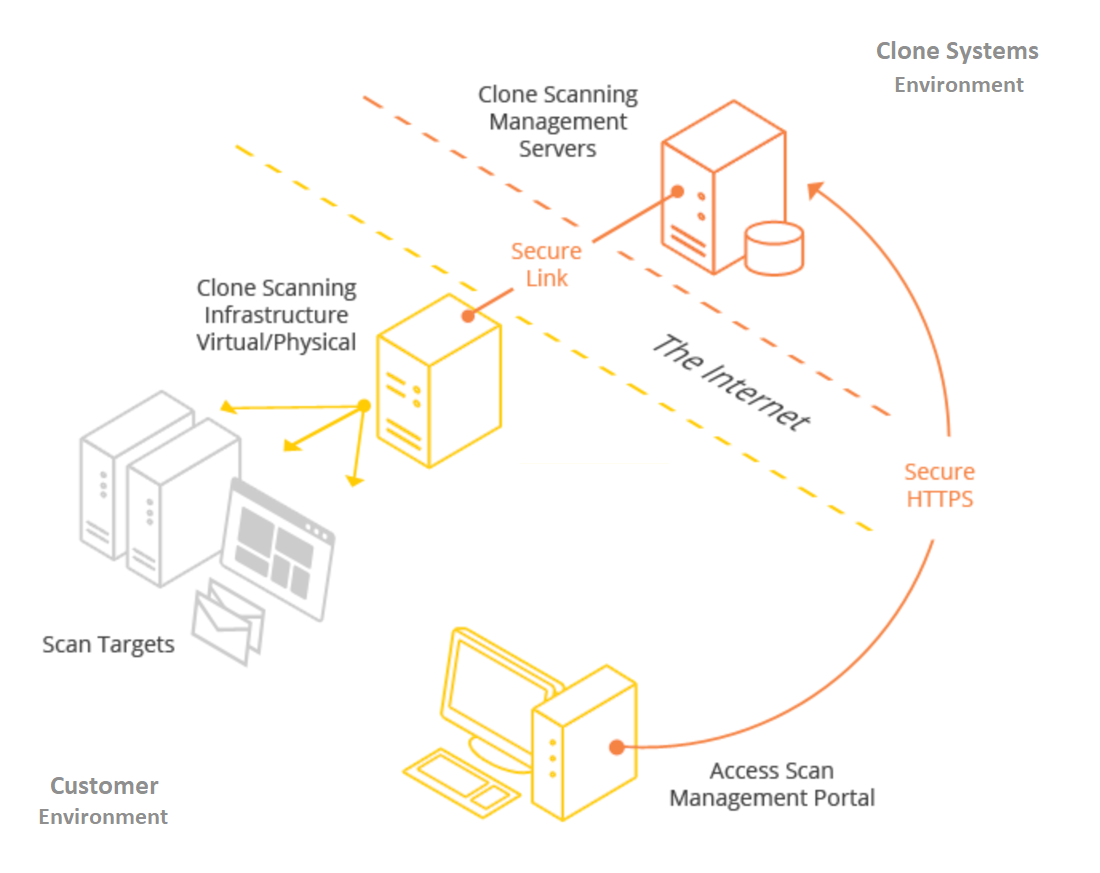
Internal Vulnerability Scanning
Internal vulnerability scanning requires setting up a security scanning server within your network. Physical and virtual options exist. (VMware, VirtualBox, Microsoft Hyper-V, and Citrix XEN, to name a few) Perform full credentialed or partial un-credentialed scans against your assets.
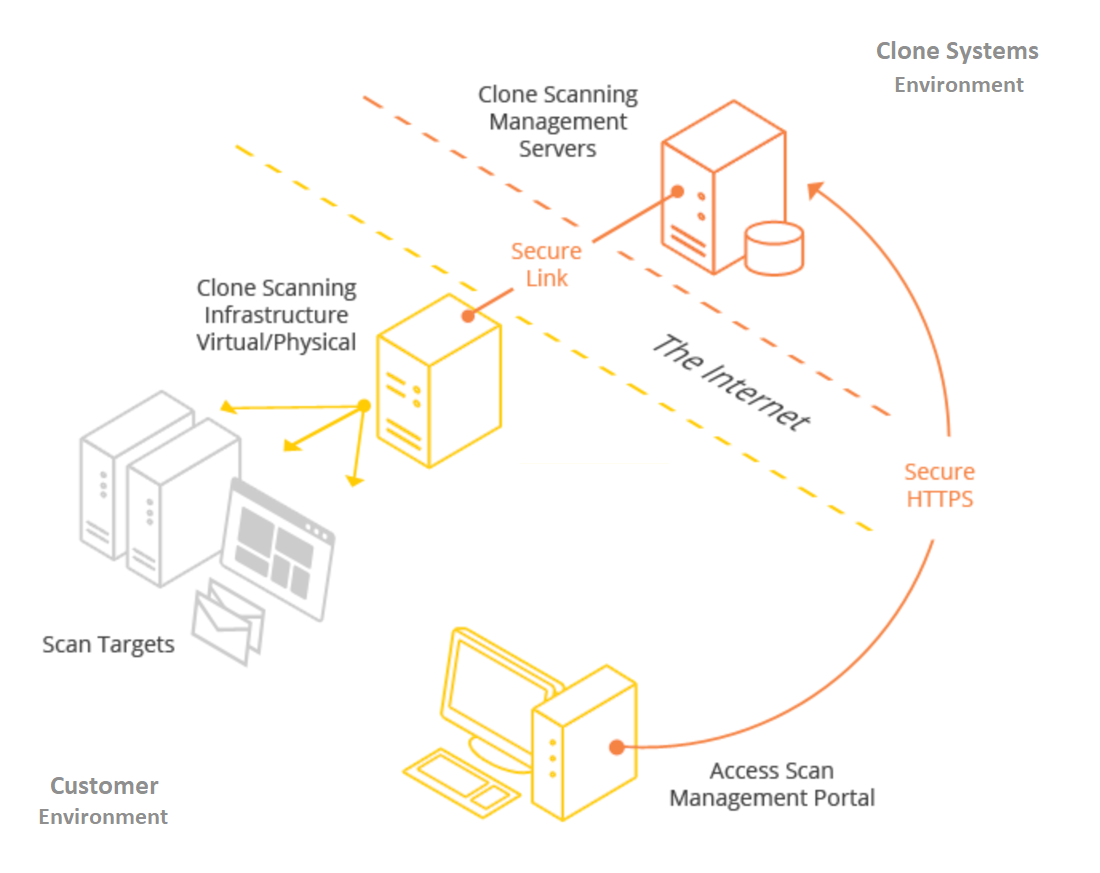
Internal Vulnerability Scanning
Internal vulnerability scanning requires setting up a security scanning server within your network. Physical and virtual options exist. (VMware, VirtualBox, Microsoft Hyper-V, and Citrix XEN, to name a few) Perform full credentialed or partial un-credentialed scans against your assets.
45M+
Vulnerability Checks
Performed Daily
7M+
Vulnerabilities
Uncovered Daily
21K+
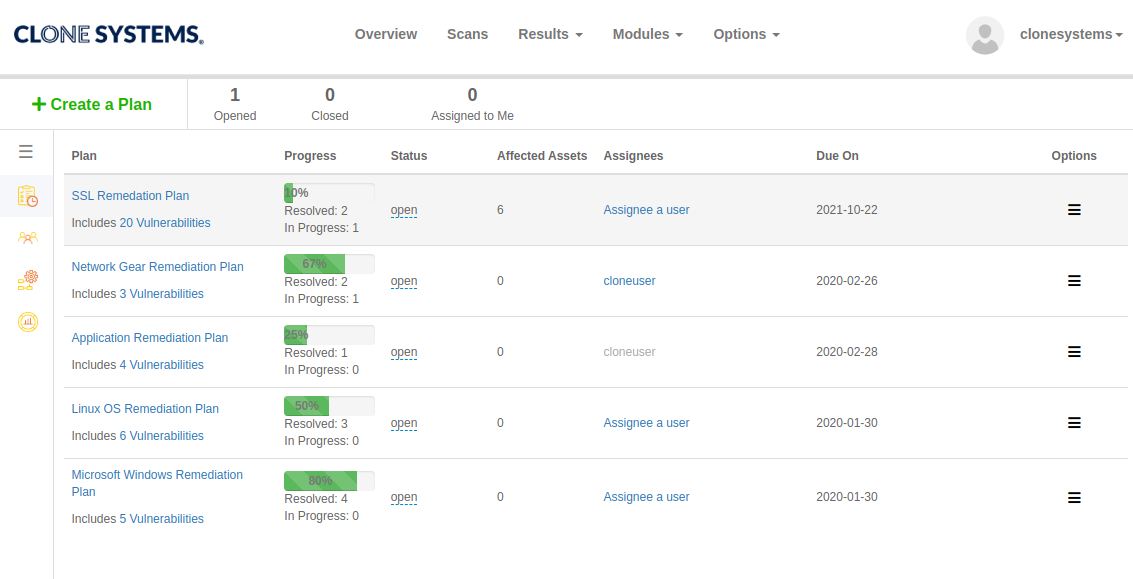
Remediations
Performed Weekly
400+
New Signatures
Added Monthly
Perform Internal & External Vulnerability scans
Evaluate your infrastructure’s security to identify vulnerabilities and obtain recommendations to improve security.
Perform Internal & External Vulnerability scans
Evaluate your infrastructure’s security to identify vulnerabilities and obtain recommendations to improve security.
Easy to use self-managed web-based scanning portal
Perform internal & external vulnerability scans
Detailed reports display all risks and threats