Bridging the SOC 2 Gap: Why Auditors Need Independent Technical Testing to Verify Your Security
As service organisations race to deliver software and collect data, many view a System and Organization Controls (SOC 2) report as the gold standard for…
As service organisations race to deliver software and collect data, many view a System and Organization Controls (SOC 2) report as the gold standard for…
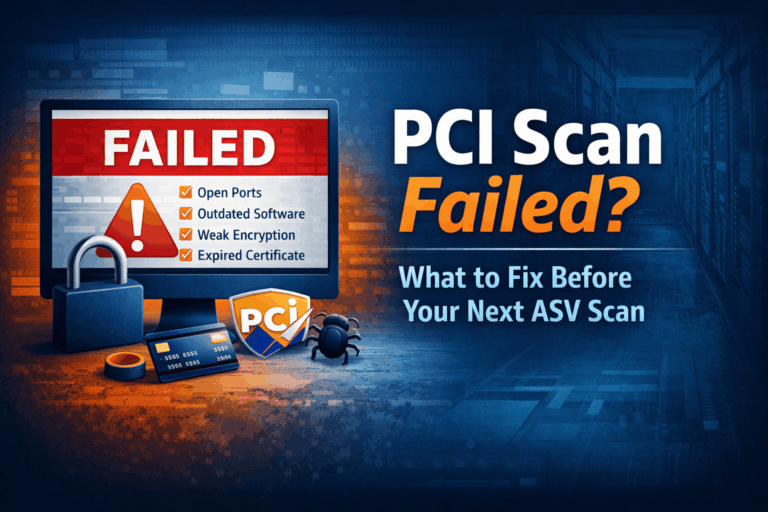
Failing a PCI scan is more common than most organizations expect. A failed ASV scan typically occurs when external systems expose vulnerabilities that violate…
When someone searches for a PCI scan, PCI scanning, ASV scan, PCIASV scan or PCI compliance, they are usually looking for two things: a…

The digital supply chain is no longer just a convenience. It’s a battleground. And as businesses become more reliant on interconnected vendors and software,…

What is an Approved Scanning Vendor (ASV)? An Approved Scanning Vendor (ASV) is an organization that utilizes security services and tools to conduct external…
Ethical hacking is critical for determining how well-prepared organizations are to avoid, detect, and respond to emerging attack methods.
